- Course
Salesforce Sharing and Security Fundamentals
Security and record sharing is at the core of any successful organization and many Salesforce certification exams. This course will teach you about the essential skills permissions, profiles, secure code, and sharing on the Salesforce platform.
- Course
Salesforce Sharing and Security Fundamentals
Security and record sharing is at the core of any successful organization and many Salesforce certification exams. This course will teach you about the essential skills permissions, profiles, secure code, and sharing on the Salesforce platform.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
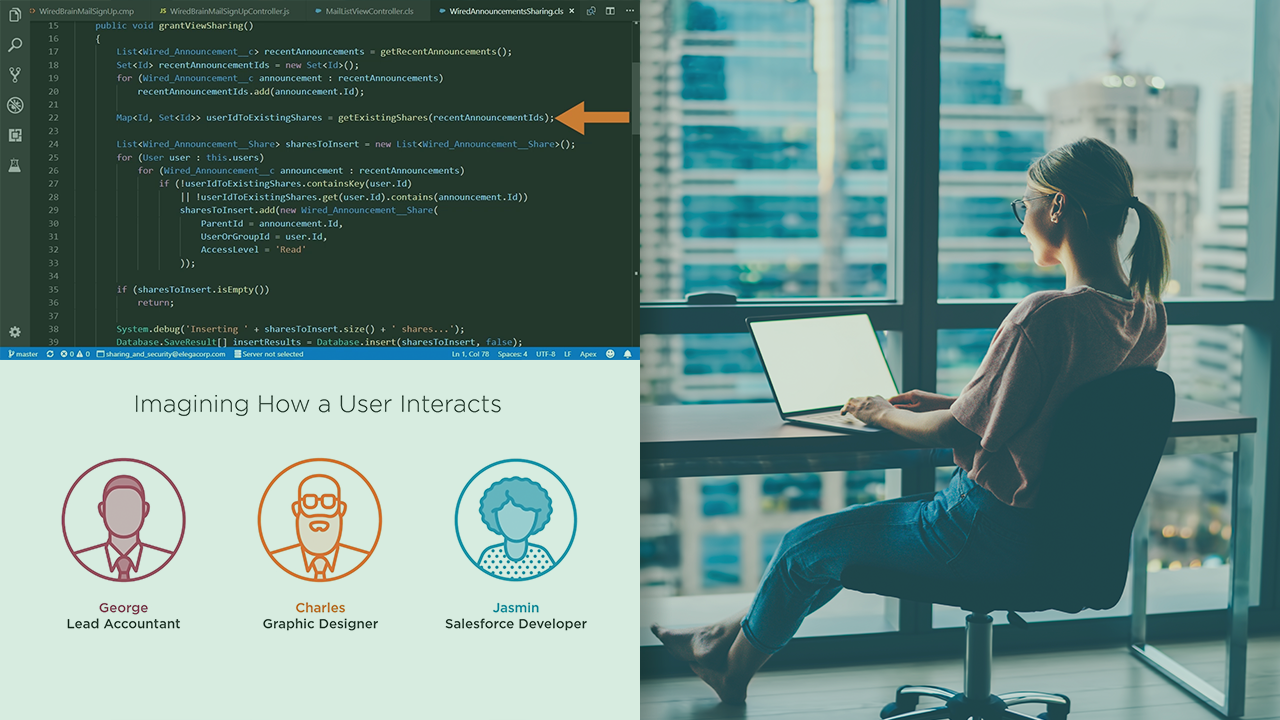
Salesforce sharing and security is at the core of any successful enterprise or organization, and to many Salesforce certification exams. In this course, Salesforce Sharing and Security Fundamentals, you will learn foundational knowledge of security on the Salesforce platform. First, you will learn about users and user controls like password policies and IP login range restrictions. Next, you will discover the declarative security functionality like profiles, permission sets, and row level record sharing. Finally, you will explore how to write more secure code on the platform considering common vulnerabilities. When you’re finished with this course, you will have the skills and knowledge of security needed to perform a meaningful audit and make improvements to any Salesforce Org.

