- Course
Secure Coding: Using Components with Known Vulnerabilities
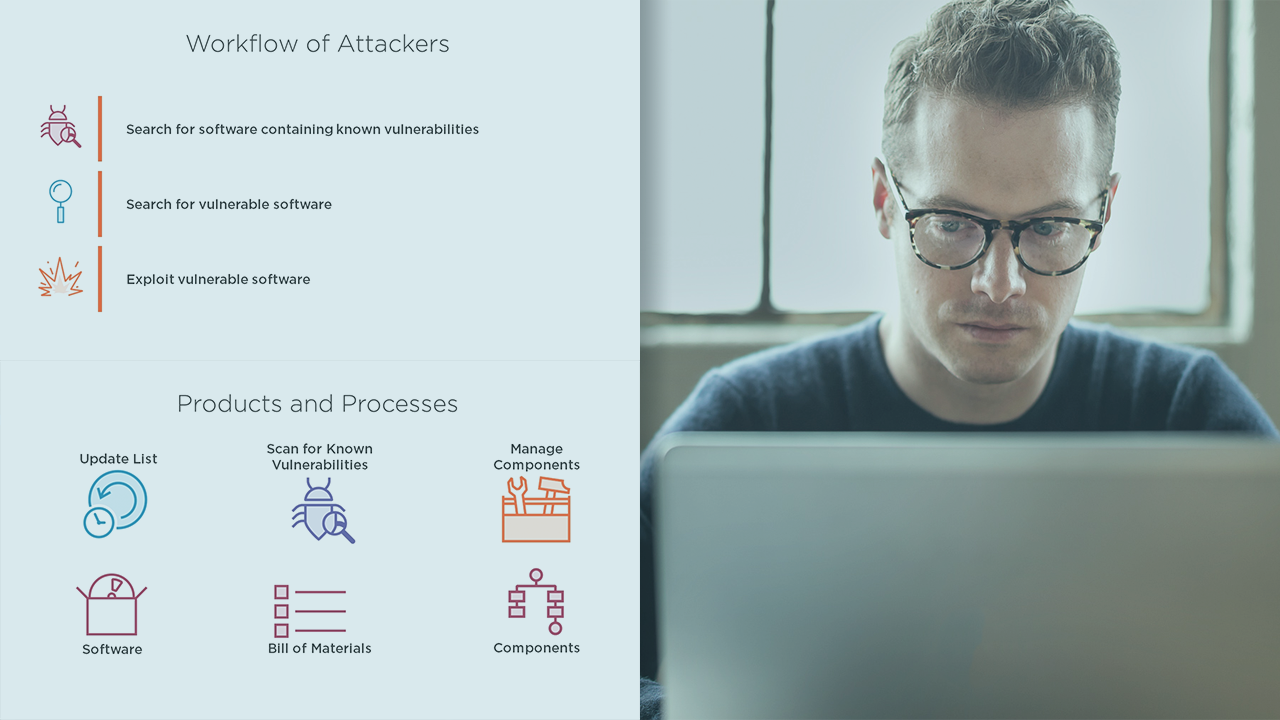
This course explains the risk of using components with known vulnerabilities. It outlines tools and strategies to reduce the overall risk. The course also discusses several methods to enhance the overall security when using third party components.
- Course
Secure Coding: Using Components with Known Vulnerabilities
This course explains the risk of using components with known vulnerabilities. It outlines tools and strategies to reduce the overall risk. The course also discusses several methods to enhance the overall security when using third party components.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Do you know if old components you are using are up to date, or contain published vulnerabilities? This course teaches you all about how to reduce the risk when using third-party components. First, you will learn about how to combine the abundance of open source software and component re-use. Next, you will discover how to achieve faster time to market with a plethora of languages, frameworks and package managers. Finally, you will learn about the patch management process. By the end of this course, you will know how to take a methodical approach towards reducing the risk, from installation and versioning all the way to virtual patching and software composition analysis.

