- Course
Secure Couchbase 6 Clusters
Security in Couchbase spans a variety of topics, and this course focuses on the most important ones - user authentication and authorization, auditing activities, redacting sensitive data, and encrypting communications.
- Course
Secure Couchbase 6 Clusters
Security in Couchbase spans a variety of topics, and this course focuses on the most important ones - user authentication and authorization, auditing activities, redacting sensitive data, and encrypting communications.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Data
What you'll learn
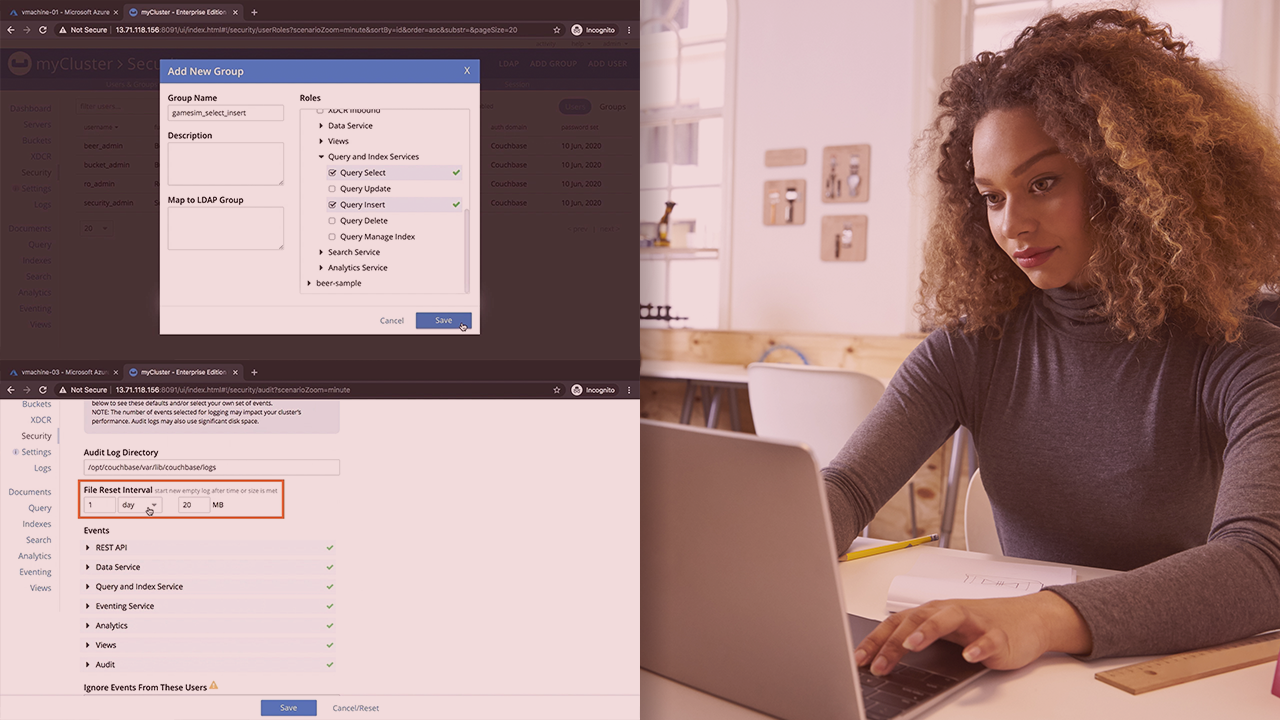
Once you begin scaling out your Couchbase cluster, the security of your database begins to take on more importance. In this course, Secure Couchbase Clusters, you'll explore the most crucial factors related to security and privacy in Couchbase. First, you'll discover Role-based access control (RBAC) and how it applies to the management of users, groups, and roles in Couchbase. Next, you'll learn about user management from the UI and how this can be achieved programmatically using the Couchbase CLI and the REST API. Then, you'll delve into the auditing feature in Couchbase and how this can be used to track the activities of users and the occurrence of a variety of events on a cluster. After that, you'll develop an understanding of the encryption settings such as cipher suites, and how to enable a node-to-node encryption. Finally, you'll explore the creation and installation of custom certificates to secure communications on a cluster. By the end of this course, you'll be well-versed in the options available to manage security on a Couchbase cluster - from ensuring that the right people have the right degree of access, that sensitive information is well-protected, and that network traffic to and from your cluster is secured.
Secure Couchbase 6 Clusters
-
Version Check | 15s
-
Course Prerequisites and Outline | 2m 17s
-
Role-based Access Control (RBAC) in Couchbase | 4m 33s
-
Demo: Setting up a Cluster | 5m 39s
-
Demo: Creating Users from the UI | 4m 8s
-
Demo: Testing Cluster-level Admin Roles | 8m 13s
-
Demo: Testing Bucket-level Admin Roles | 3m 34s
-
Demo: Creating a Group of Users | 7m 9s

