- Course
Securing Applications on AWS
Learn how to use CloudWatch for monitoring, CloudTrail for auditing, Config for resource compliance, and Trusted Advisor for warnings. Explore how to protect against DDOS attacks with the WAF and use the API Gateway for creating and hosting APIs.
- Course
Securing Applications on AWS
Learn how to use CloudWatch for monitoring, CloudTrail for auditing, Config for resource compliance, and Trusted Advisor for warnings. Explore how to protect against DDOS attacks with the WAF and use the API Gateway for creating and hosting APIs.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
- Security
What you'll learn
Many applications at AWS are over-hosted. In this course, Securing Applications on AWS, you will gain knowledge about how to protect over-hosted applications at AWS using a variety of powerful management tools provided by Amazon.
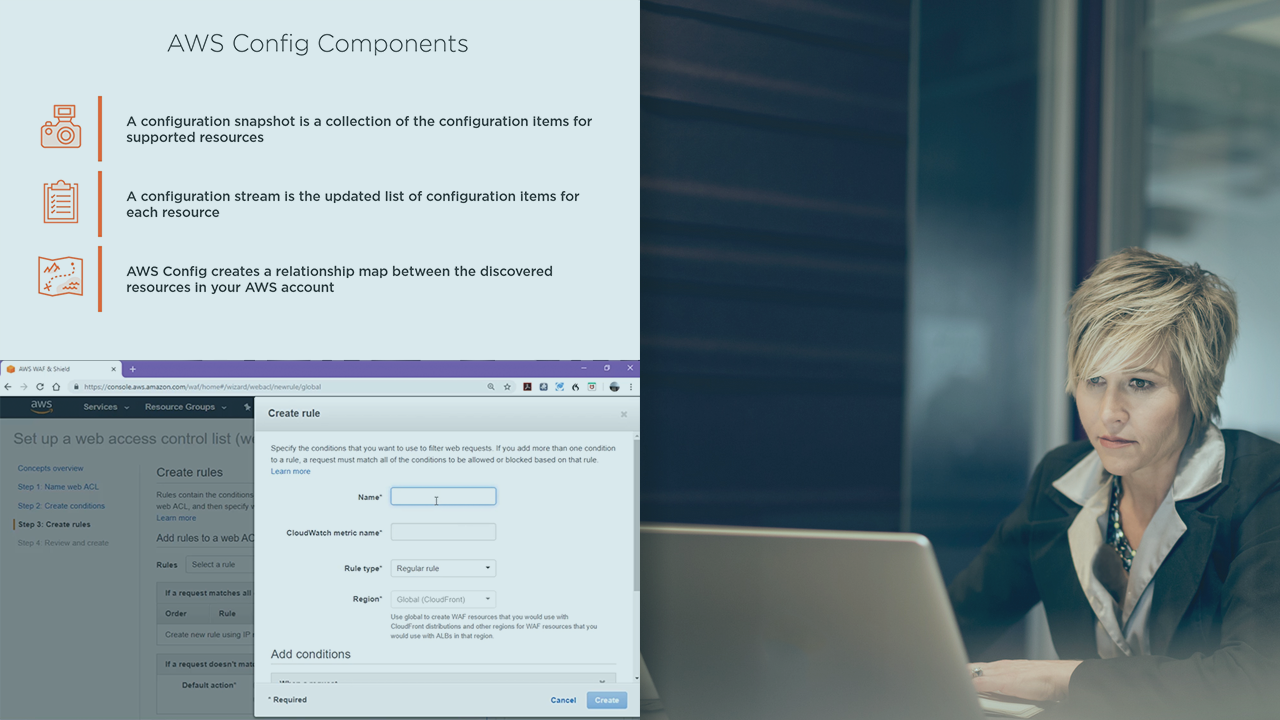
First, you will look at the Web Application Firewall (WAF) and see how to protect against unwanted access from incoming public traffic, you will explore the API Gateway and how you can create and host APIs at AWS, and you will dive into Amazon Cognito which allows you to create user and identity pools that allow internal and external authentication and single sign-on access.
Next, you will look at the operation of CloudWatch and its use of metrics which allow you to manage all of your AWS resources, as well as CloudTrail which helps to monitor all activity in your AWS account.
Finally, you will see how to use TrustedAdvisor to alert you to account issues, and AWS Config to set rules for managing your infrastructure resources.
When you are done with this course, you will know how to monitor, audit, protect, and take many other actions towards protecting your applications hosted on AWS.

