- Course
Securing AWS Infrastructure
This course will teach you how to secure your hosted AWS infrastructure. You will learn about securing your EC2 instances and how to create additional threat protection layers using managed AWS services to manage and secure your applications.
- Course
Securing AWS Infrastructure
This course will teach you how to secure your hosted AWS infrastructure. You will learn about securing your EC2 instances and how to create additional threat protection layers using managed AWS services to manage and secure your applications.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
- Security
What you'll learn
Securing AWS infrastructure is an ongoing task, with many moving parts.
In this course, Securing AWS Infrastructure, you’ll find the best methods of securing your hosted applications at AWS.
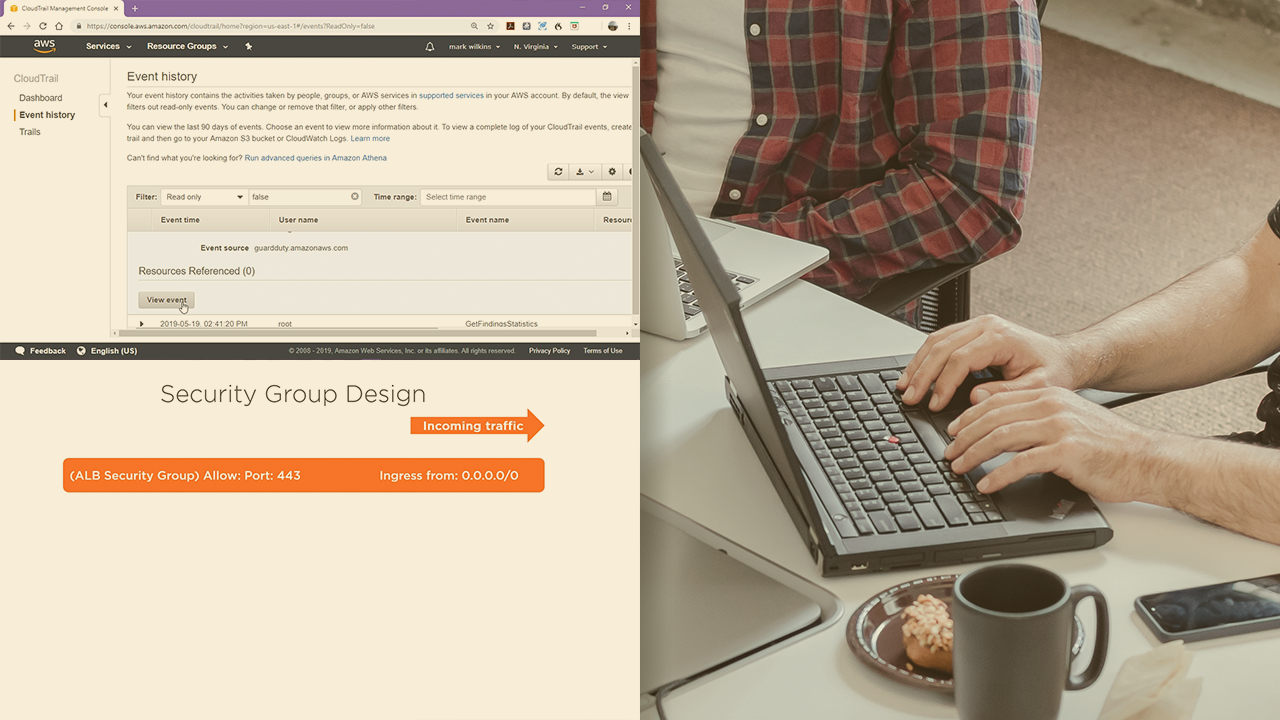
First, you'll learn the best subnet and IP address types to host your applications, and how to plan out VPC security using route tables, security groups, and Network ACLs.
Next, you’ll discover the roles that redundancy and availability play in application security, looking at load balancing and autoscaling and how they help your applications to remain available.
Finally, you’ll explore the intrusion detection and prevention available at AWS for all customers, specifically how to create threat protection layers with Web Application Firewall, AWS Shield, Shield Advanced, and the AWS Firewall manager. You’ll also see how to protect public-facing resources using CloudFront.
You'll also go through the use of GuardDuty and Amazon Inspector. This course’s content is a mix of lecture and hands-on demos.
When you’re finished with this course, you will understand how to properly secure your infrastructure components at AWS.

