- Course
Securing Windows 10: Data at Rest, in Use, and in Transit
Prevent your data from leaking and minimize threats to your data's security. In this course, you will learn about how leaks occur and the software and hardware tools available within Windows 10 that can help mitigate any security risks.
- Course
Securing Windows 10: Data at Rest, in Use, and in Transit
Prevent your data from leaking and minimize threats to your data's security. In this course, you will learn about how leaks occur and the software and hardware tools available within Windows 10 that can help mitigate any security risks.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
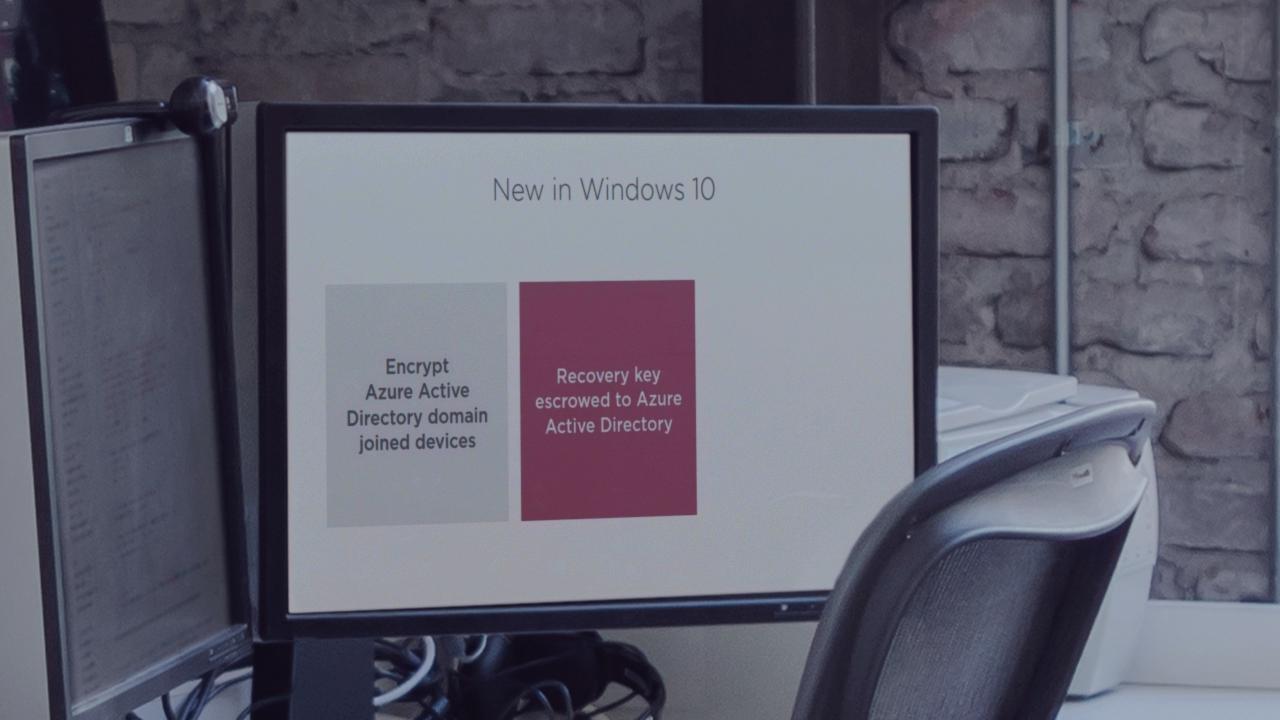
Security threats will never go away; in fact, they are becoming more prevalent than ever. So, how do you mitigate security risks in this day and age? The answer? Windows 10. The new hardware and software capabilities unleashed will help protect your data from modern threats, and ultimately provide a secure environment. In this course, Securing Windows 10: Data at Rest, in Use, and in Transit, you will learn how to protect your data at any stage. First, you'll examine how data can leak and how to use BitLocker to protect your resting data. Next, you'll cover Dynamic Access Control from a client perspective and how to prevent co-mingling in your Windows data. Finally, you'll learn how to use the Secure Socket Tunneling Protocol (SSTP) and its VPN functionality as well as the client functionality of RMS encryption to secure data in transit. By the end of this course, you'll be able to secure your own data from multiple kinds of risks and attacks.

