- Course
Security Event Triage: Leveraging Existing Security Device Alerts
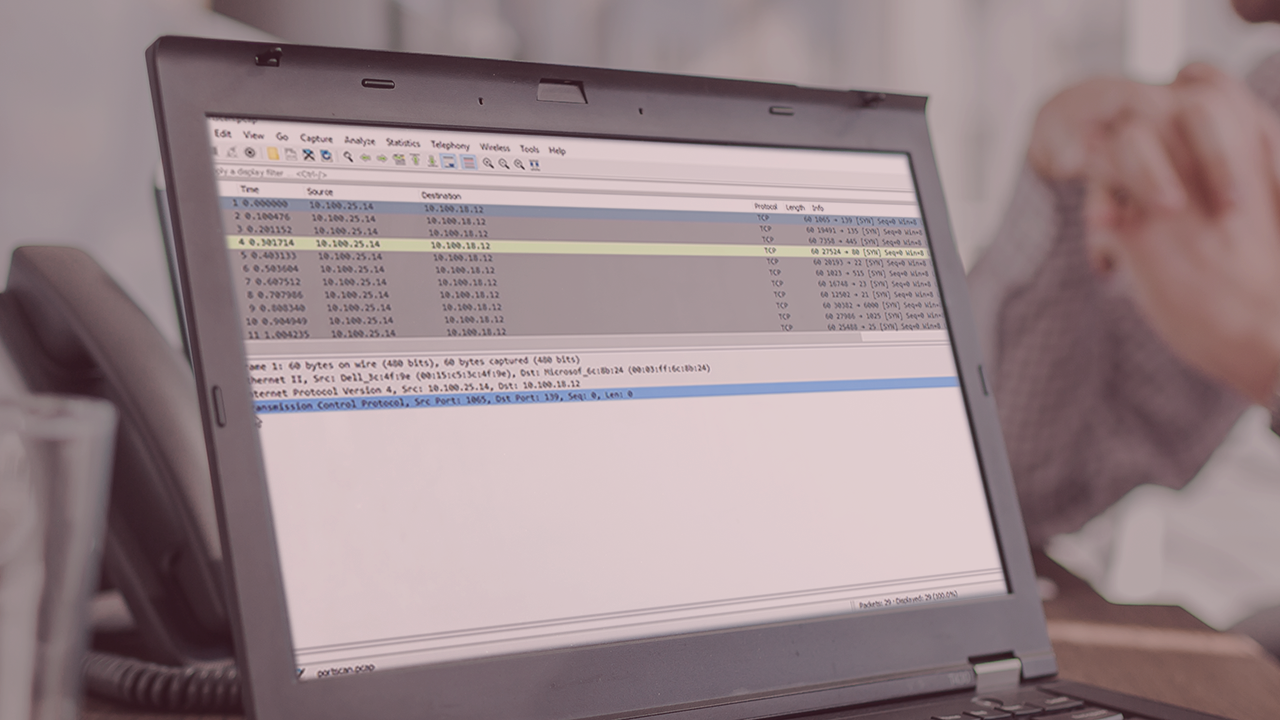
Identifying suspicious network activity can prevent serious security breaches. By monitoring centralized device logs you can catch potential security problems in a timely manner.
- Course
Security Event Triage: Leveraging Existing Security Device Alerts
Identifying suspicious network activity can prevent serious security breaches. By monitoring centralized device logs you can catch potential security problems in a timely manner.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Identifying suspicious activity on your network can be achieved by analyzing security device logs. In this course, Security Event Triage: Leveraging Existing Security Device Alerts, you'll learn how to analyze security device logs looking for security problems. First, you'll learn about network security devices and the relationship between the OSI model and the ability to decipher the meaning of network traffic captures. Next, you'll see how to analyze firewall logs to identify abnormal activity which could indicate a security compromise, and how analyzing network access control (NAC) logs can identify questionable host and network connectivity for unauthenticated as well as authenticated devices. Finally, you'll explore how to use cloud-based methods such as cloud packet capturing and centralized security monitoring to identify potential security problems in the cloud. When you're done with this course, you'll have the foundational knowledge of continuous monitoring and interpretation of correlated log events needed to gain the best possible picture of network security events.


