- Course
Splunk Enterprise Administration: Managing Users and Authentication
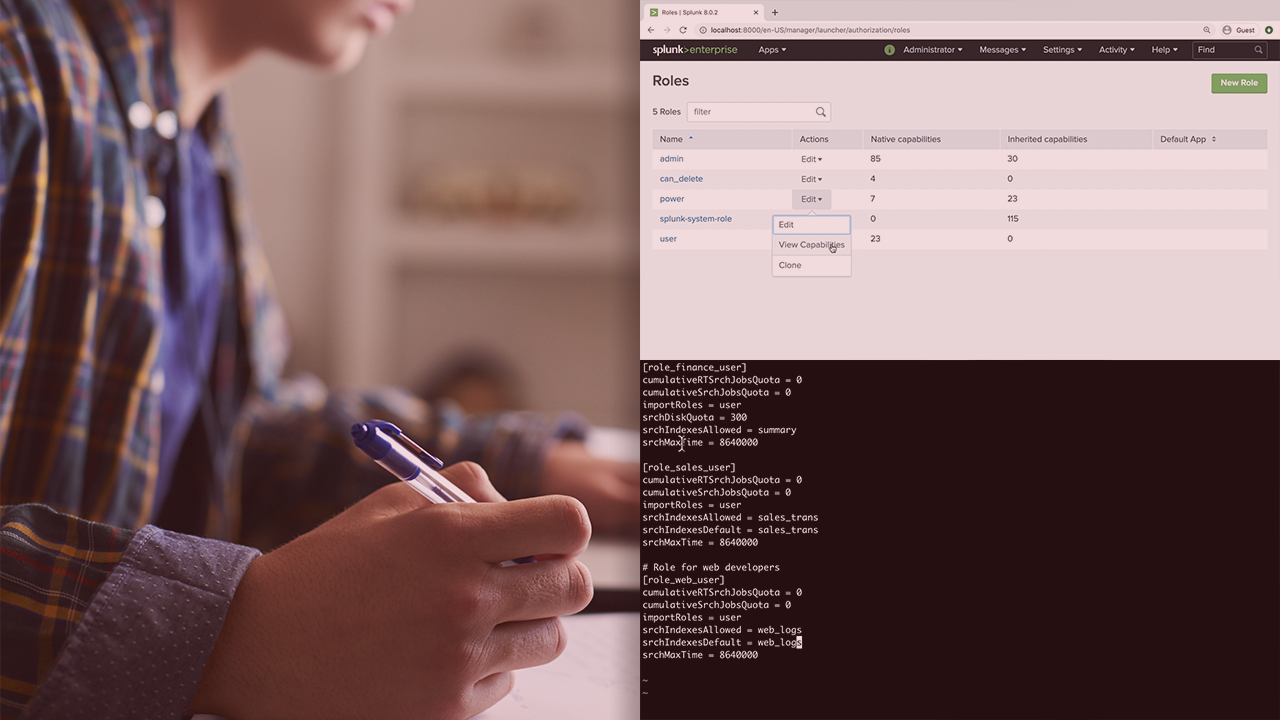
Splunk's role based access control implementation can be daunting to learn. In this course, you'll gain a thorough understanding of Splunk roles and master Splunk authentication methods including single sign-on and multi-factor authentication.
- Course
Splunk Enterprise Administration: Managing Users and Authentication
Splunk's role based access control implementation can be daunting to learn. In this course, you'll gain a thorough understanding of Splunk roles and master Splunk authentication methods including single sign-on and multi-factor authentication.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Securing Splunk Enterprise is an important task of a Splunk Administrator. But mastering Splunk's role based access control and various authentication mechanisms can be difficult. In this course, Splunk Enterprise Administration: Managing Users and Authentication, you will gain foundational knowledge of Splunk users and roles management. First, you will learn Splunk's role based access control and the inheritance of capabilities. Next, you will discover configuring external LDAP for authentication and mapping LDAP groups into Splunk roles. Finally, you will explore how to configure single sign-on and multi-factor authentication. When you’re finished with this course, you will have the skills and knowledge of configuring Splunk roles and authentication mechanisms needed to manage Splunk security.

