- Course
Spring Security 5: Authentication / Authorization - Building Effective Layers of Defense
Spring Security is one of the most popular frameworks for securing Java applications. In this course, you will learn what makes it so powerful by configuring it with Spring Boot and adding multi-factor Authentication and Authorization to pages
- Course
Spring Security 5: Authentication / Authorization - Building Effective Layers of Defense
Spring Security is one of the most popular frameworks for securing Java applications. In this course, you will learn what makes it so powerful by configuring it with Spring Boot and adding multi-factor Authentication and Authorization to pages
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
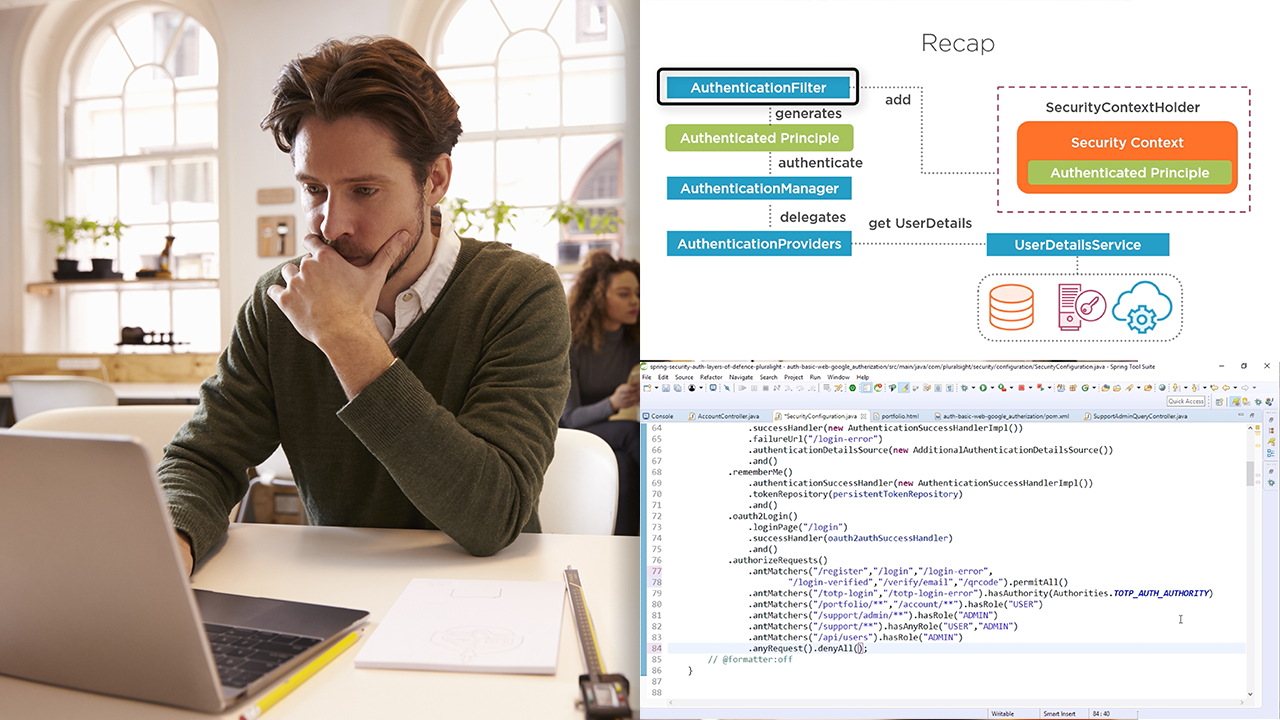
Getting security wrong can have major repercussions for you, your organization, and your users. In this course, Spring Security 5: Authentication / Authorization - Building Effective Layers of Defense, you will learn what's under the covers, the architecture and components, and how they can be configured to provide a Defense-in-Depth solution to contain and limit the impact of any security breaches. First, you will explore how to configure Spring Security within Spring Boot and add multi-factor authorization using basic, digest, HTTPS, 2FA, additional security questions, and email verification. Next, you will learn the effects of configuring security incorrectly and how to secure your secrets and users credentials. Finally, you will discover how to outsource authorization with Oauth2 social login and how to add authorization to your pages, URLs, methods, and domain objects with security configuration, expressions, and annotations. When you are finished with this course, you will have a foundational knowledge of how to effectively configure Authentication and Authorization with Spring Security that will help you as you move forward to building more robust security solutions for your applications.

