- Course
SQL Server 2016 New Features for Developers
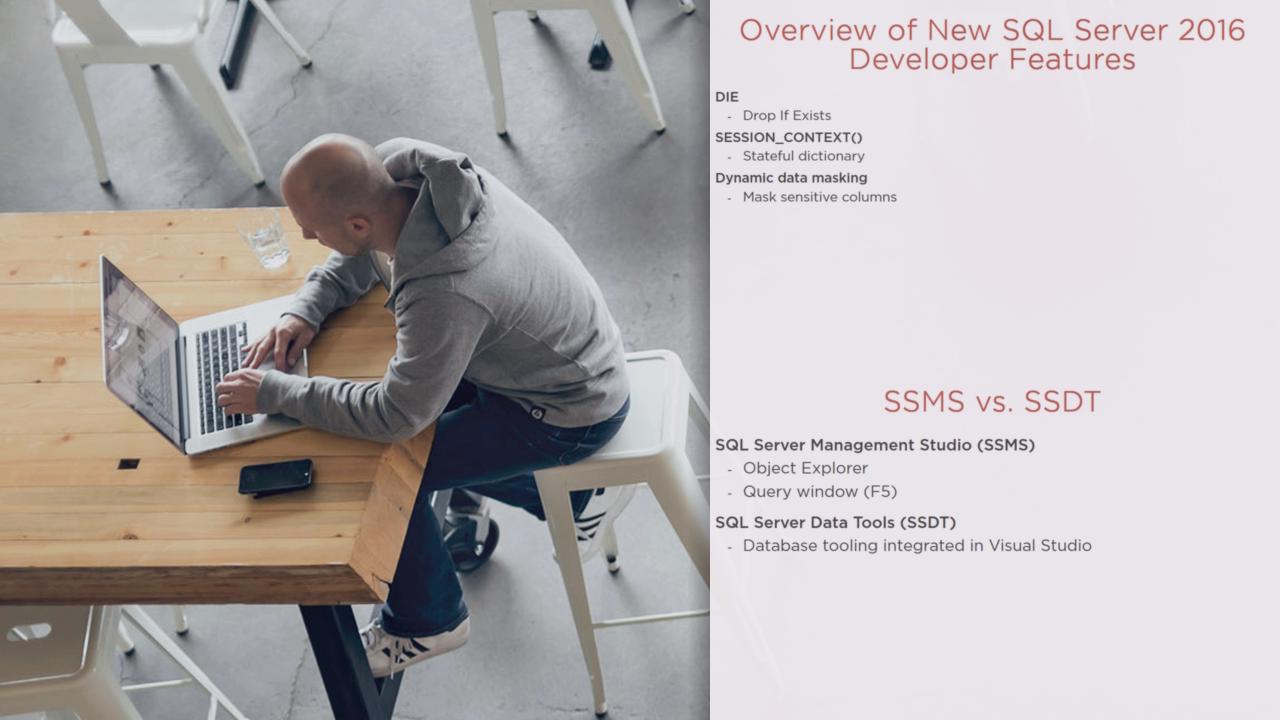
This course teaches the new developer features in SQL Server 2016, including Drop If Exists (DIE), SESSION_CONTEXT, dynamic data masking (DDM), row-level security (RLS), Always Encrypted, stretch database, temporal data, and built-in JSON support.
- Course
SQL Server 2016 New Features for Developers
This course teaches the new developer features in SQL Server 2016, including Drop If Exists (DIE), SESSION_CONTEXT, dynamic data masking (DDM), row-level security (RLS), Always Encrypted, stretch database, temporal data, and built-in JSON support.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Data
What you'll learn
This demo-packed course, SQL Server 2016 New Features for Developers, teaches the many powerful features for developers that have been added in SQL Server 2016. First, you'll discover new security features such as dynamic data masking (DDM), row-level security (RLS), and Always Encrypted. Next, you'll learn about the innovative capabilities, including "stretch" database (allow select tables in an on-premises database to be transparently relocated in Azure SQL Database), and temporal data (enable "time travel" to access data as it existed at any point in time). You'll also learn about the new built-in Javascript Object Notation (JSON) support which enables bi-directional manipulation of JSON data in SQL Server. By the end of this course, you'll be ready for SQL Server 2016 and its exciting new developer features.

