- Course
Threat Hunting with Yara
With the battle on cyber threats becoming an uphill battle for current security capabilities, Threat Hunting with Yara will uplift your skills for detecting and defending against modern threats.
- Course
Threat Hunting with Yara
With the battle on cyber threats becoming an uphill battle for current security capabilities, Threat Hunting with Yara will uplift your skills for detecting and defending against modern threats.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
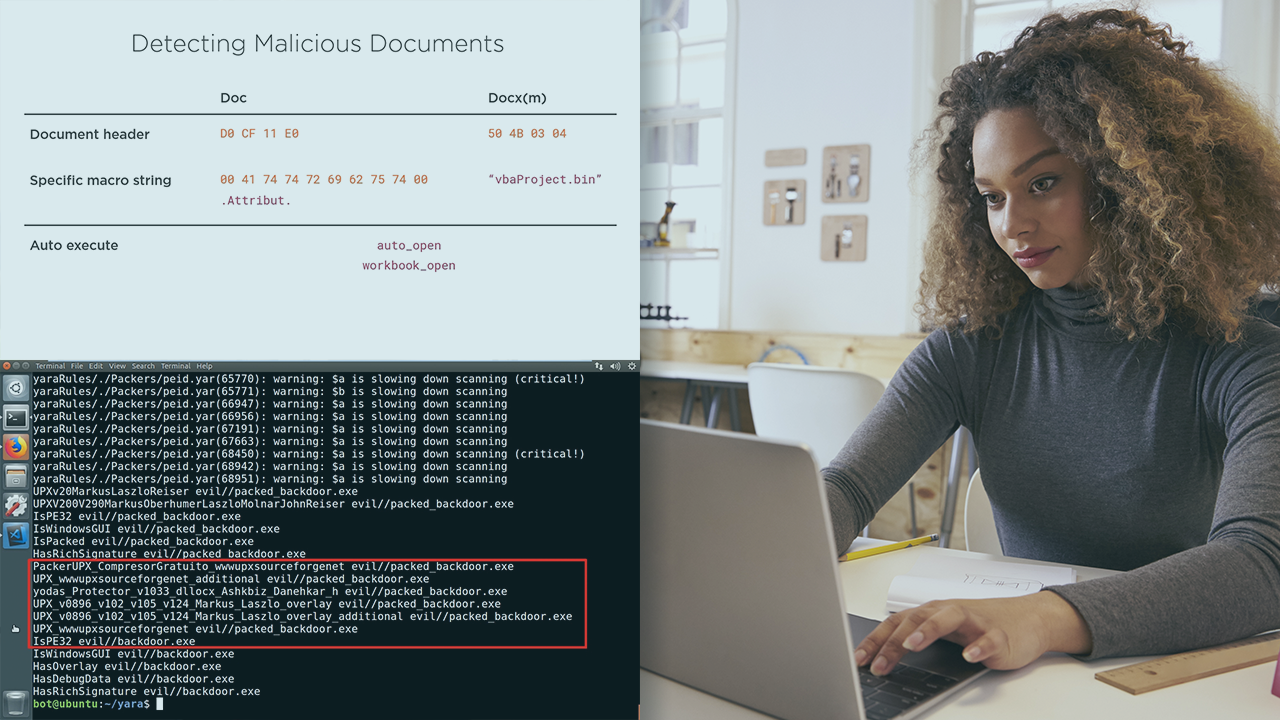
Traditional hash-based detections are lagging behind when it comes to advanced malware threats. In this course, Threat Hunting with Yara, you will gain the ability to use Yara to identify and clarify malicious artifacts. First you will discover how to write effective rules, next you will craft detections based on patterns identified in suspicious binaries, finally you will explore hunting at scale strategies using Yara rules with other security capabilities. When you're finished with this course, you will have the skills and the knowledge of hunting for threats with Yara when responding to security incidents.

