- Course
Understanding the Java Virtual Machine: Security
This course covers the details of code security explaining how the SecurityManager and the AccessController work together to grant permissions to code in the current call stack. We cover how to grant permissions based on policy and how to create your own permissions and also cover how to limit the stack walk so that privileged code can run.
- Course
Understanding the Java Virtual Machine: Security
This course covers the details of code security explaining how the SecurityManager and the AccessController work together to grant permissions to code in the current call stack. We cover how to grant permissions based on policy and how to create your own permissions and also cover how to limit the stack walk so that privileged code can run.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
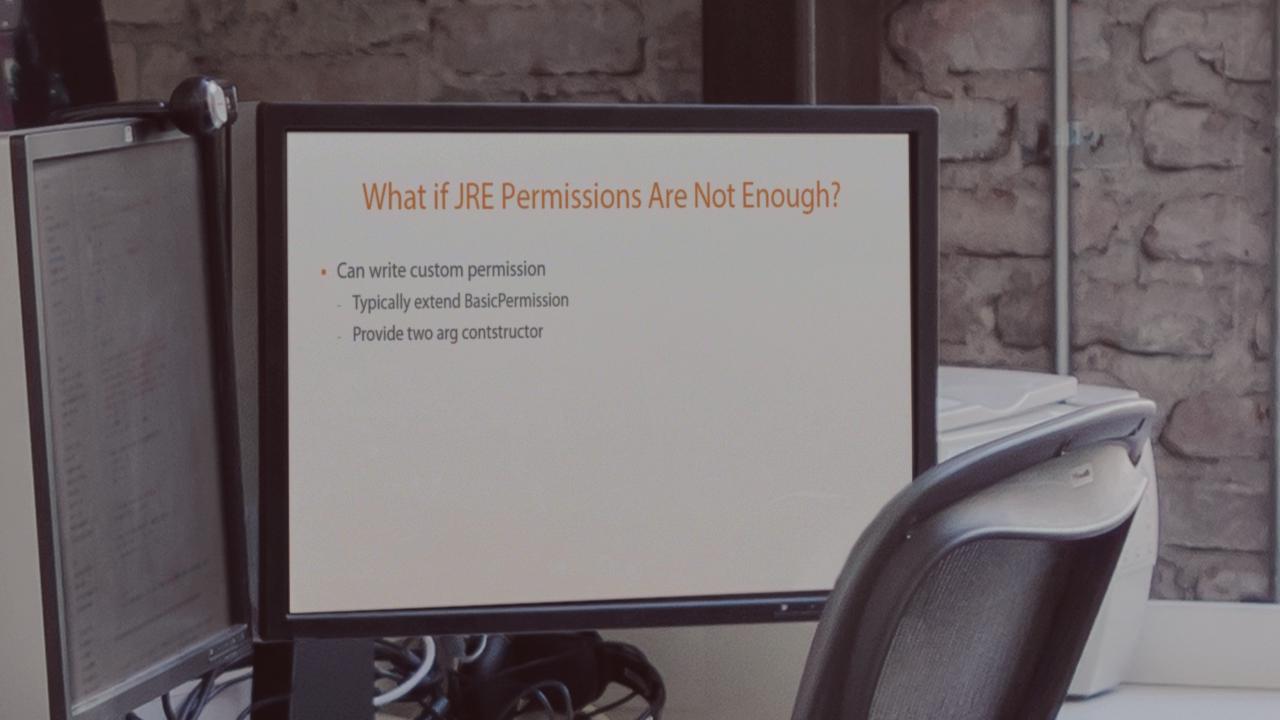
Java security is built around the idea of permissions and policy. Code is granted permissions based on the currently in-force policy. In this course, we look at how the security manager and access controller work hand-in-hand to provide this security. The course covers how to set a security manager and how to set up and edit a policy file to grant the levels of permissions that code needs. Permissions are typically based on where code is loaded from but we also look at how to sign code, so that permissions can be based on who created a library. The course also looks at how the AccessController walk the call stack to check that a permission can be granted. While the JRE comes with a set of permissions, these are not always enough so the class covers creating and using your own permissions. Finally we cover the idea of 'privileged scope' which allows code to be granted some permission even when code around them should cause the grant to fail.

