- Course
Vulnerability Management with Qualys Cloud Platform
Managing and remediating vulnerabilities is one of the most important tasks in cybersecurity. In this course, we will explore how to use the Qualys Cloud Platform to implement a full vulnerability management program.
- Course
Vulnerability Management with Qualys Cloud Platform
Managing and remediating vulnerabilities is one of the most important tasks in cybersecurity. In this course, we will explore how to use the Qualys Cloud Platform to implement a full vulnerability management program.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
What you'll learn
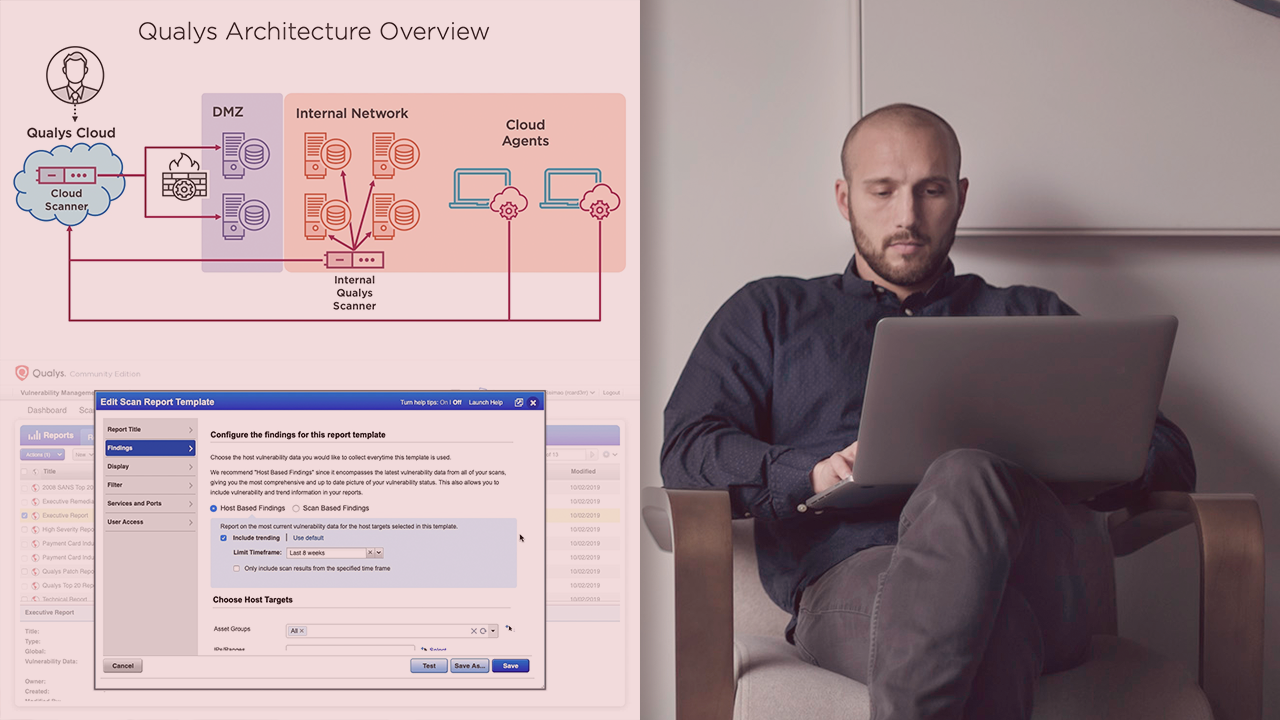
Vulnerable applications and insecure configurations are some of the top attack vectors for hackers, and it only takes one vulnerability to have a whole company compromised. In this course, Vulnerability Management with Qualys Cloud Platform, you will learn how to use the Qualys Cloud Platform to identify and manage the vulnerabilities in your company. First, you will explore the Qualys architecture and how to deploy the Qualys scanners in your environment. Then, you will discover how to scope and plan your vulnerability management program. Finally, you will learn how to configure scans and reports in Qualys, create proper vulnerability remediation plans, and investigate zero-day vulnerabilities with Qualys. When you are finished with this course, you will have the knowledge of how to deploy a full vulnerability management program, from configuring scanners to generating executive reports. Software required: Qualys Cloud Enterprise Edition or Qualys Cloud Community Edition (Free version)

