- Course
Web Application Penetration Testing: Weak Cryptography
Cryptography is used to secure modern web applications. The problem is that quite many things can go wrong and weak cryptography can lead to very severe consequences. That’s why this subject is interesting for penetration testers.
- Course
Web Application Penetration Testing: Weak Cryptography
Cryptography is used to secure modern web applications. The problem is that quite many things can go wrong and weak cryptography can lead to very severe consequences. That’s why this subject is interesting for penetration testers.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
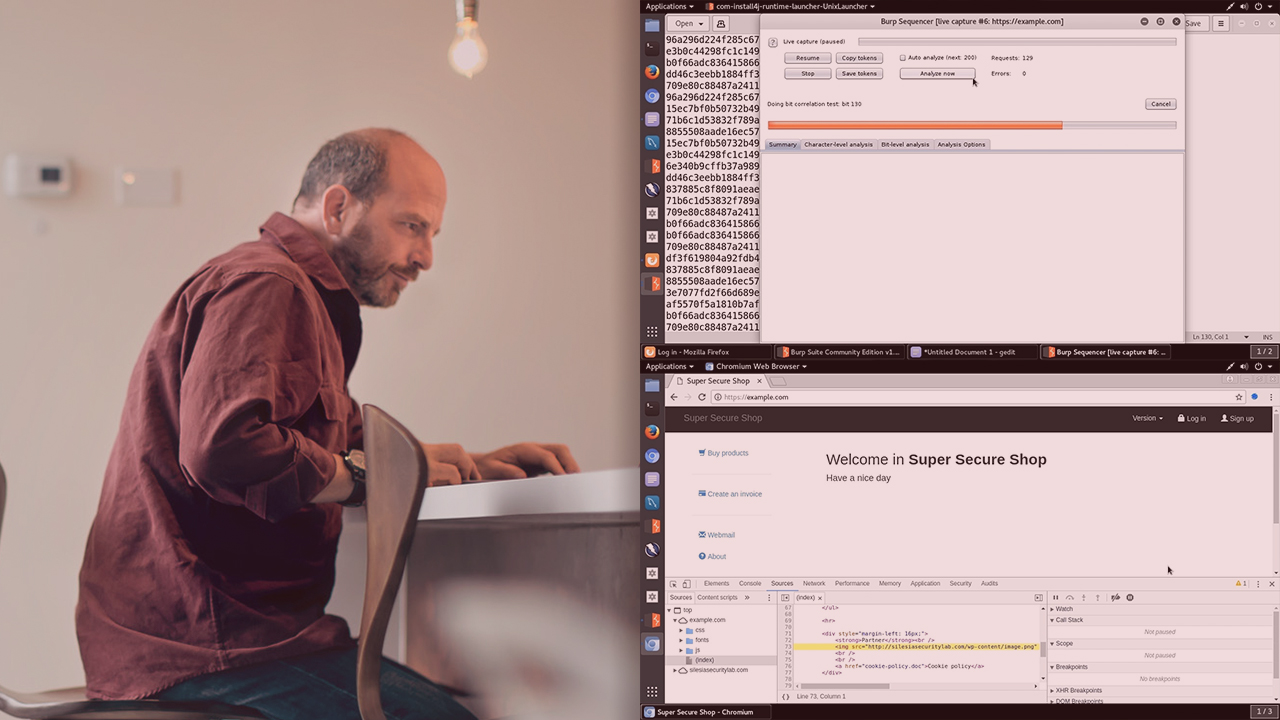
Weak cryptography can lead to very severe consequences. In this course, Web Application Penetration Testing: Weak Cryptography, you will learn how to test for weak cryptography in modern web applications. First, you will learn about HTTPS enforcement and insecure cookie processing. You will see that users’ credentials can be disclosed over insecure channel when HTTPS enforcement is not implemented in the web application. You will also see a demonstration in which a cookie with sensitive data can be disclosed over insecure channel, even if secure HTTPS is enforced in the web application. Next, you will explore Transport Layer Protection, Heartbleed vulnerability, and mixed content vulnerability. You will see how to check if Transport Layer Protection is configured securely in your web application, and how the attacker can read sensitive data from the memory of the web server as a result of Heartbleed vulnerability (which is one of the most famous vulnerabilities in crypto libraries). You will also see what dangers can happen when there is mixed content vulnerability in your web application. Finally, you will discover session randomness analysis, insecure password storage, and Sub-resource Integrity Protection. You will see how you can analyze the randomness of session IDs in your web application with Burp Suite Sequencer. You will learn why you should store a hash of the password (instead of the password in plaintext) and how it can solve your problems with insecure password storage. You will also learn how Subresource Integrity can be used to protect the integrity of scripts and style sheets in your web applications. By the end of this course, you will know how severe consequences can happen as a result of weak cryptography and you will also know how to test for weak cryptography in modern web applications.

