- Course
Web Application Penetration Testing: Business Logic Testing
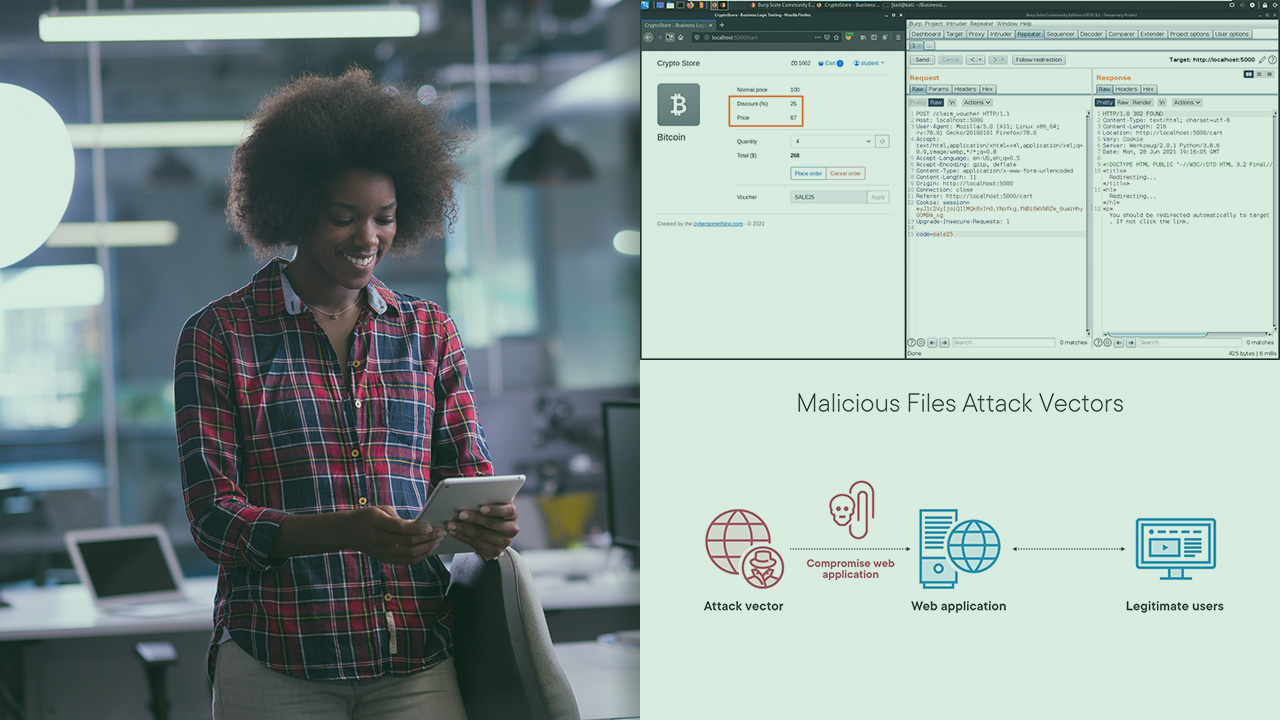
Business logic flaws are context specific and very hard for automated tools to discover. This course will teach you how to identify and exploit business logic vulnerabilities.
- Course
Web Application Penetration Testing: Business Logic Testing
Business logic flaws are context specific and very hard for automated tools to discover. This course will teach you how to identify and exploit business logic vulnerabilities.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Web Applications are sometimes designed based on flawed assumptions about how business logic should work, using the application in unintended ways may result in outstanding security vulnerabilities with a critical business impact . In this course, Web Application Penetration Testing: Business Logic Testing, you’ll learn to assess business logic flaws in modern web applications. First, you’ll explore scoping, and how to get the relevant business logic context of the application. Next, you’ll discover how to exploit business logic flaws based on the OWASP WSTG. Finally, you’ll learn how to identify and advise on bad design practices. When you’re finished with this course, you’ll have the skills and knowledge of business logic testing needed to assess the security of web applications.

