- Course
Wireshark Configuration for Cyber Security Analysis
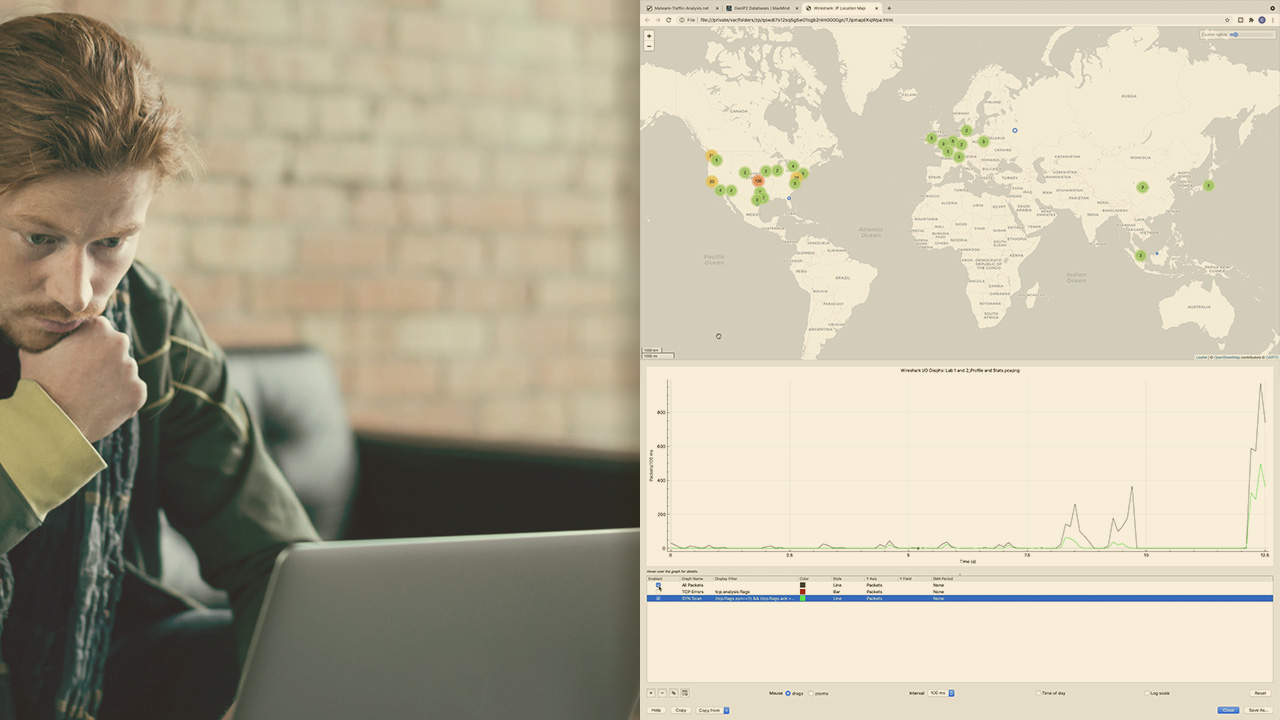
This course will teach you the best settings and filters to use in Wireshark for quickly spotting malware behavior, enumeration and scans, and other suspect traffic.
- Course
Wireshark Configuration for Cyber Security Analysis
This course will teach you the best settings and filters to use in Wireshark for quickly spotting malware behavior, enumeration and scans, and other suspect traffic.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Properly configuring Wireshark can greatly help to track down IoCs and can reduce the time required for Cyber Security professionals to perform network forensics. In this course, Wireshark Configuration for Cyber Security Analysis, you’ll learn to quickly spot suspect traffic with Wireshark. First, you’ll explore the top five Wireshark settings that all Security Professionals should implement when analyzing traffic. Next, you’ll discover how to create filters and coloring rules that will make suspect traffic stand out. Finally, you’ll learn how to decrypt TLS traffic for analyzing secure communications. When you’re finished with this course, you’ll have the skills and knowledge of Wireshark needed to speed up traffic analysis and incident response.
Wireshark Configuration for Cyber Security Analysis
-
Introduction to Cyber Security Analysis with Wireshark | 2m 42s
-
Lab 1 - Creating a Security Profile | 7m 22s
-
Lab 2 - The Statistics View | 5m 16s
-
Lab 3 - Configuring GeoIP Location Resolution | 5m 31s
-
Lab 4 - Configuring Custom Columns | 4m 42s
-
Lab 5 - Configuring Name Resolution | 5m 28s
-
Lab 6 - Exporting HTTP Objects and Files | 3m 23s
-
Lab 7 - Reassembling and Exporting FTP Files | 3m 23s
-
Module Summary | 38s

