- Course
Developing Daemons and Services Protected by Azure Active Directory
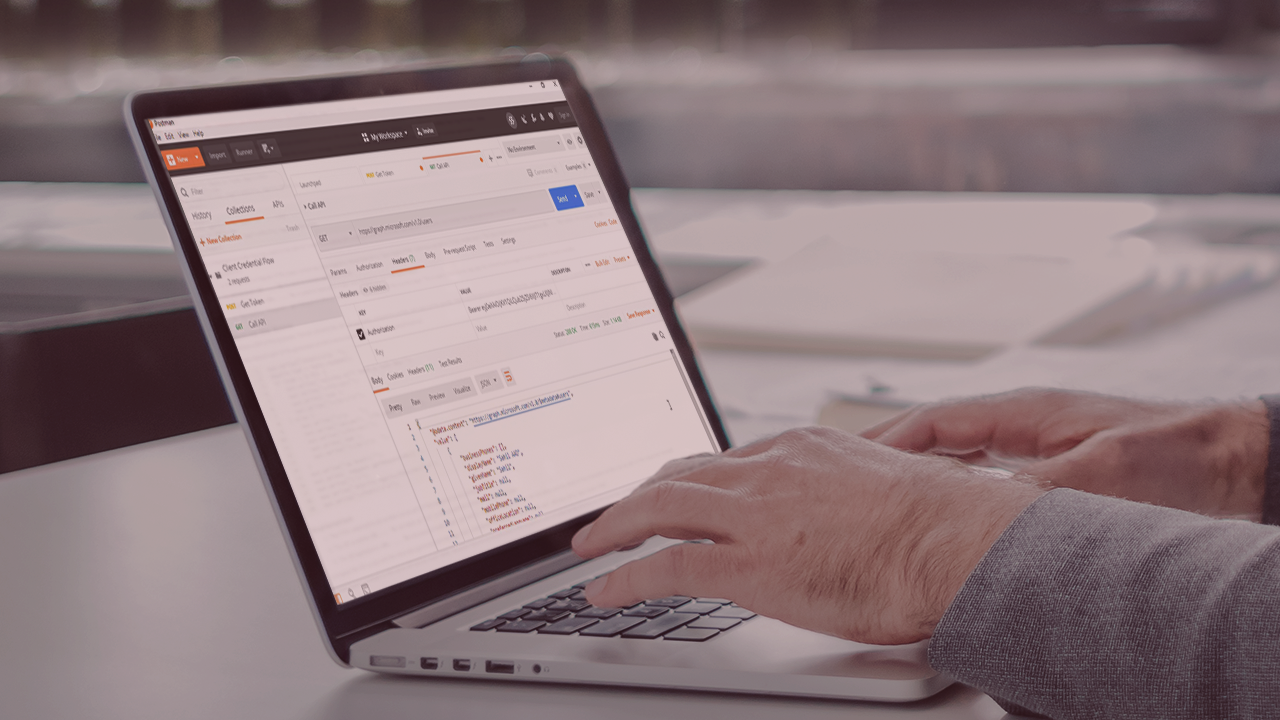
Daemons or Services are a big part of any application. This course will teach you how you can securely access Azure AD protected APIs from your services and daemons.
- Course
Developing Daemons and Services Protected by Azure Active Directory
Daemons or Services are a big part of any application. This course will teach you how you can securely access Azure AD protected APIs from your services and daemons.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
What you'll learn
Headless processes commonly referred to as daemons or services have no opportunity to present an authentication user interface. Yet they must be able to access Azure AD protected resources. In this course, Developing Daemons and Services Protected by Azure Active Directory, you’ll learn to securely call Azure AD protected APIs from headless processes. First, you’ll explore the flows available to headless applications and the basics of service principals. Next, you’ll discover how to perform client credential flow with both REST or APIs on .NET, NodeJS and Python. Finally, you’ll learn how to master managed identities when working in Azure. When you’re finished with this course, you’ll have the skills and knowledge of the various facilities Azure AD offers needed to author headless applications that need to call secure APIs in Azure.

