- Course
Ethical Hacking: Buffer Overflow
Pluralsight is not an official partner or accredited training center of EC-Council. Understanding buffer overflows can be difficult unless you know the basics. This course teaches the basics by not assuming you are a programmer or computer scientist.
- Course
Ethical Hacking: Buffer Overflow
Pluralsight is not an official partner or accredited training center of EC-Council. Understanding buffer overflows can be difficult unless you know the basics. This course teaches the basics by not assuming you are a programmer or computer scientist.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
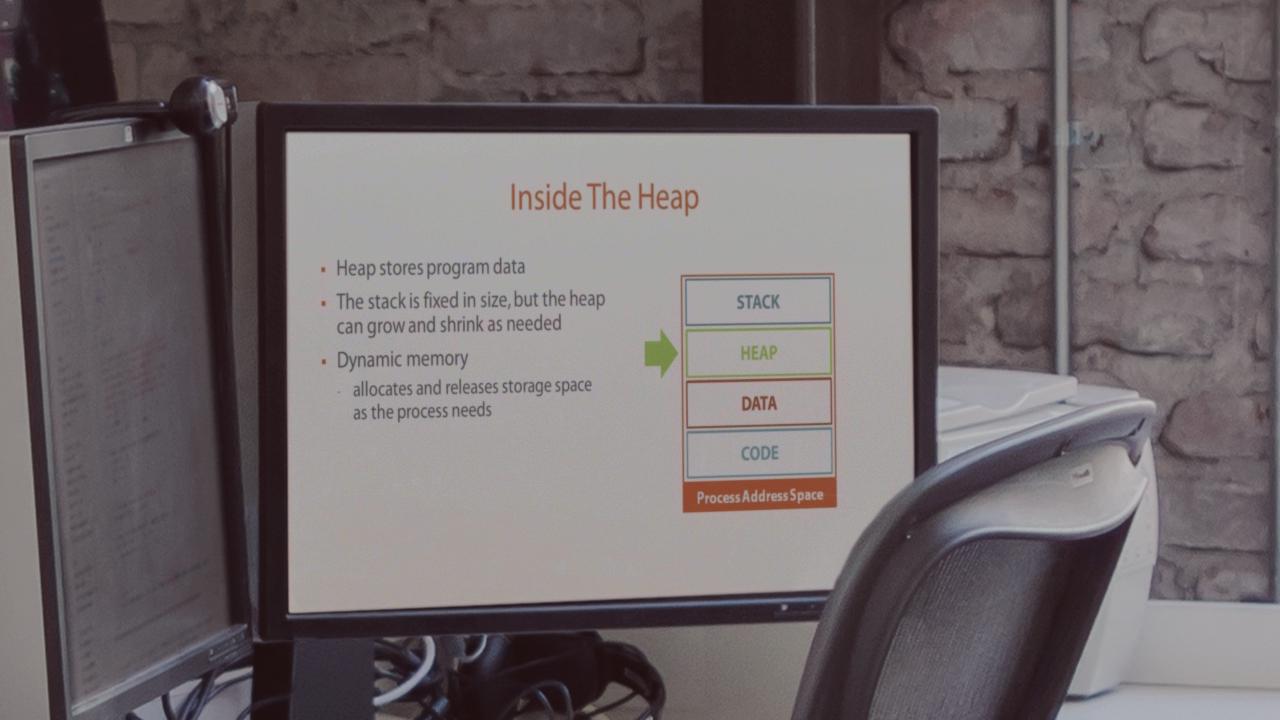
Pluralsight is not an official partner or accredited training center of EC-Council. Buffer overflow is a topic that only software developers using low-level programming languages really get an opportunity to fully understand. However, IT security professionals are increasingly called upon to better understand how vulnerabilities created by poor software design and implementation practices can be exploited to create security issues in systems and networks. The problem is that most IT professionals do not have the extensive software development background needed to tackle the subject of buffer overflow. This course breaks down the technical subjects of computer memory management, controlling code, and data inside of a running program, and exploiting poor quality software into terms that IT people with no software development experience can understand. Also examined are ways to prevent buffer overflow conditions and minimize the impact of buffer overflows that do happen. This course is part of the Ethical Hacking Series. http://blog.pluralsight.com/learning-path-ethical-hacking

