- Course
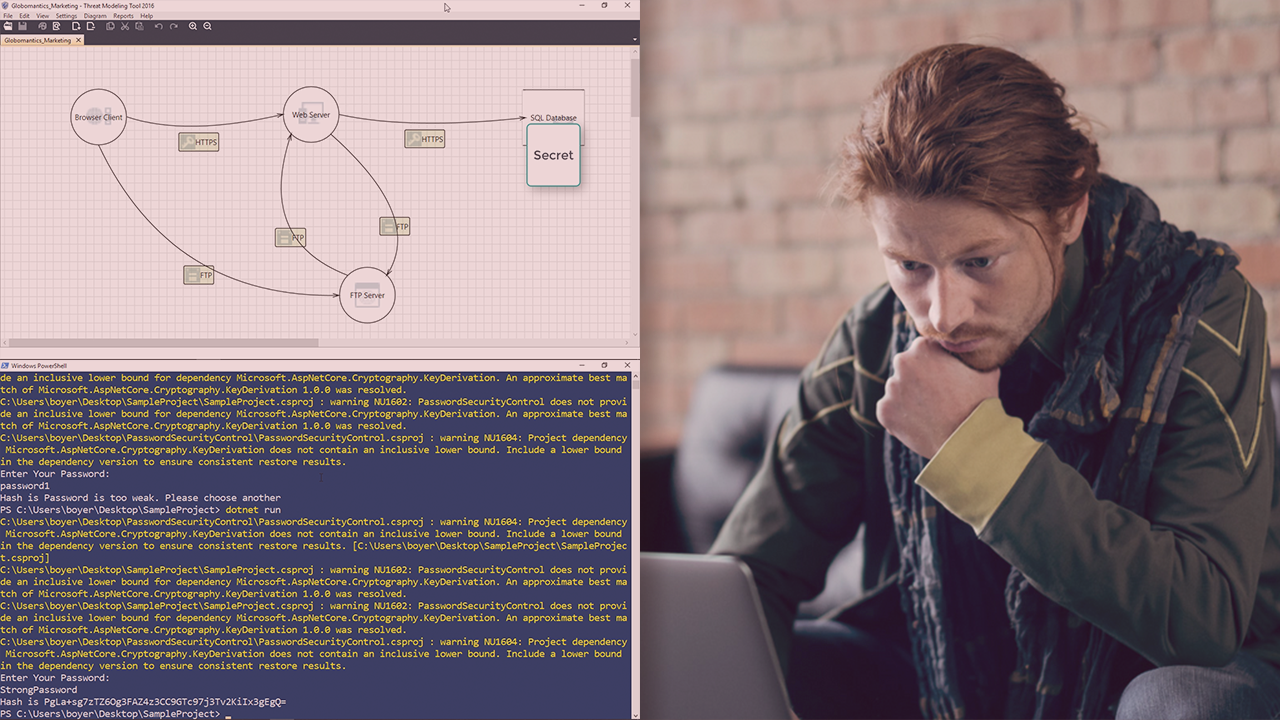
Performing Threat Modeling with the Microsoft Threat Modeling Methodology
Tired of finding security bugs after the code is written? Finding bugs late is dangerous and expensive. In this course, you'll learn techniques for threat modeling, before it's too late.
- Course
Performing Threat Modeling with the Microsoft Threat Modeling Methodology
Tired of finding security bugs after the code is written? Finding bugs late is dangerous and expensive. In this course, you'll learn techniques for threat modeling, before it's too late.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Finding security bugs after the software has been built can lead to two things: exploitation of the bug in the wild, or spending a fortune to fix it. In this course, Performing Threat Modeling with the Microsoft Threat Modeling Methodology, you will gain the ability to analyze your software and find threats to it before any line of code is written. First, you will learn how to diagram an application to clearly show how all of its parts work together. Next, you will discover how to use diagrams to find threats using techniques such as STRIDE. Finally, you will explore how to document and mitigate threats to your software. When you’re finished with this course, you will have the skills and knowledge of threat modeling needed to anticipate threats and deal with them before they cause damage.

