- Course
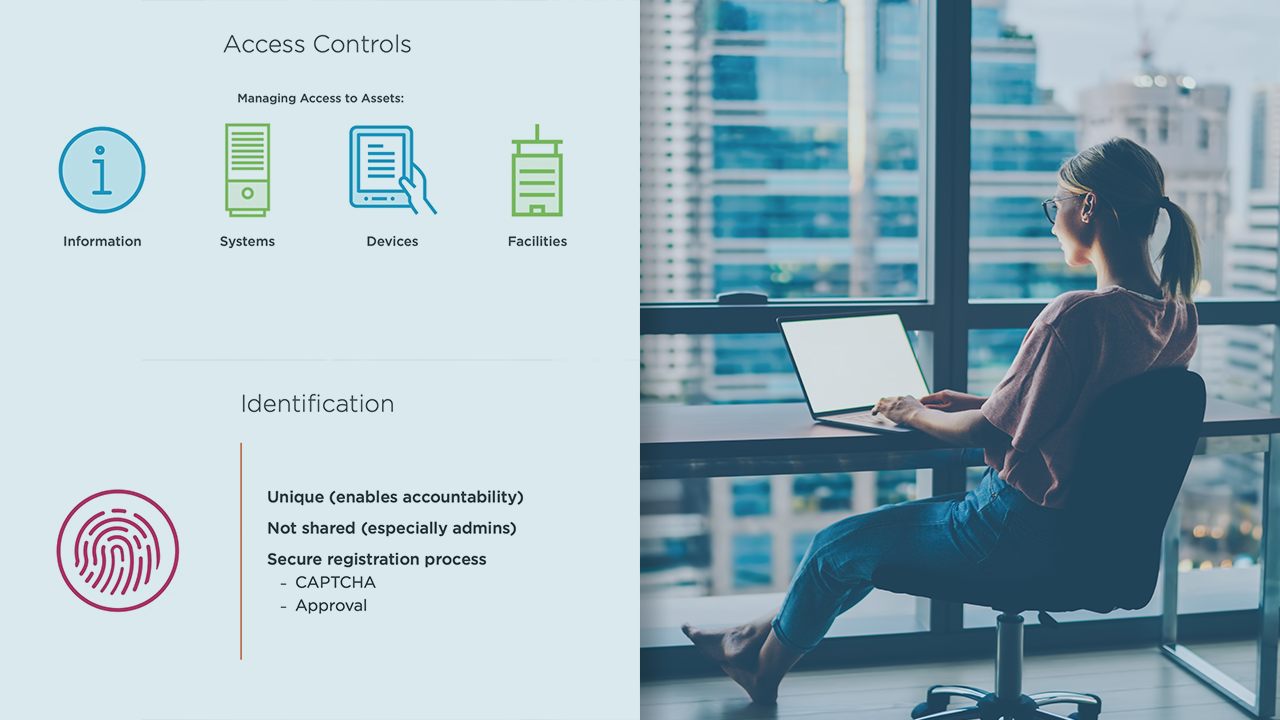
Access Control and Identity Management
Access controls are the key to protecting the assets of an organization. Access must be managed at technical, administrative, and physical levels. This course is essential for security professionals looking to gain needed knowledge and perspective.
- Course
Access Control and Identity Management
Access controls are the key to protecting the assets of an organization. Access must be managed at technical, administrative, and physical levels. This course is essential for security professionals looking to gain needed knowledge and perspective.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Access Controls and Identity Management are the heart of Information Security. In this course, Access Control and Identity Management, you will learn about the risks and challenges associated with access control concepts that a security professional must understand. First, you will discover the various access control attacks. Then, you will explore the methods of implementing and monitoring an access control system. Finally, you will learn about access control models and techniques. By the end of this course, you will know and understand the foundation of information security - access control.

