- Course
Conducting Active Reconnaissance for CompTIA PenTest+
Active reconnaissance is a necessary evil. It can sometimes alert defense teams and systems that you're snooping around, but it also helps you to see and document everything about each note on the network. Learn how to active recon the right way.
- Course
Conducting Active Reconnaissance for CompTIA PenTest+
Active reconnaissance is a necessary evil. It can sometimes alert defense teams and systems that you're snooping around, but it also helps you to see and document everything about each note on the network. Learn how to active recon the right way.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
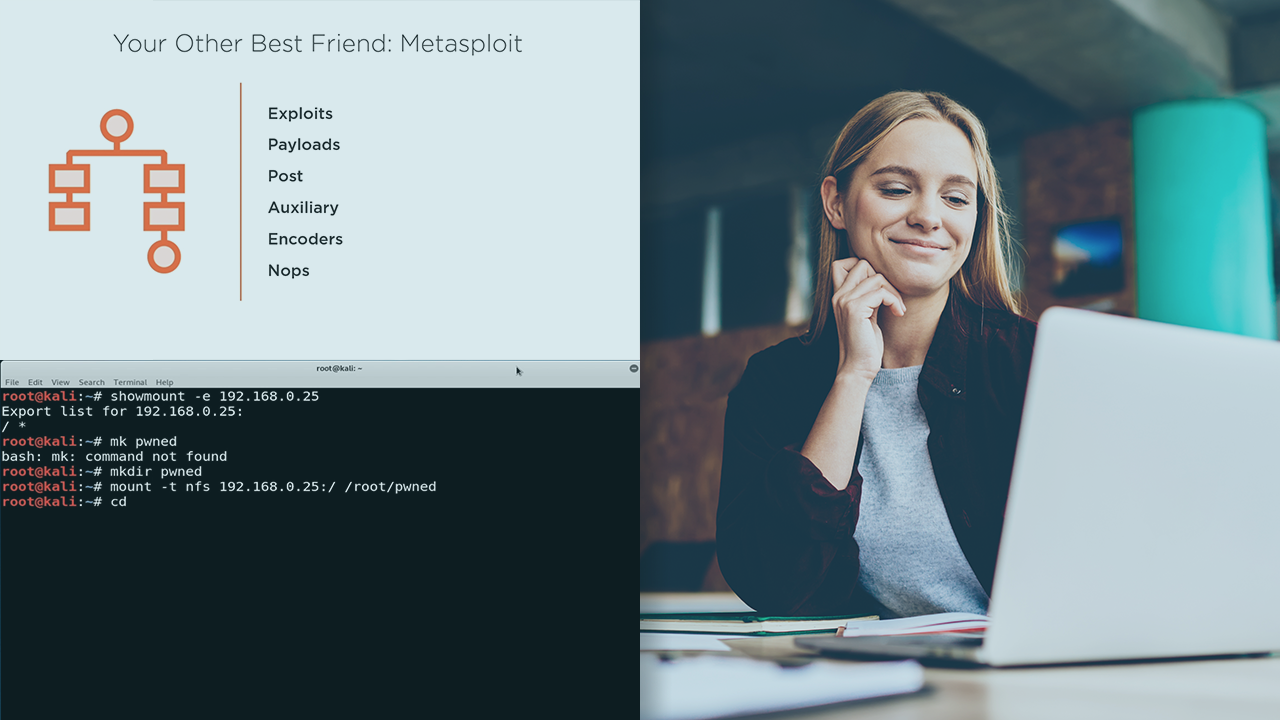
Up until now, we have been "quiet" as far as reconnaissance goes. But the downside is that many times we won't see every single system through passive methods. This is were Active Reconnaissance comes in to play.
In this course, Conducting Active Reconnaissance for CompTIA PenTest+, you will gain the ability to discover more network nodes and collect system information during your penetration tests. First, you will learn how to discover all the targets on a given network. Next, you will discover how to use enumeration to find services and even accounts on the targets. Then, you will see how to scan each one for vulnerabilities which might allow someone to gain unauthorized access to protected digital or electronic materials, and may go around routers or even firewalls to get in. Finally, you will explore how to look at different types of scripts and some cool tools to help automate your tasks.
When you’re finished with this course, you will have the skills and knowledge of discovering as many nodes, services accounts, and even some vulnerabilities needed to cover every aspect of the active reconnaissance step within any pentest engagement.

