- Course
Architecting Cisco Secure Communications
Data has become a high value commodity and protecting it is essential, especially when your data is traversing the internet and this is where VPNs come in. Using any VPN is not enough however, as picking the right solution is highly important too.
- Course
Architecting Cisco Secure Communications
Data has become a high value commodity and protecting it is essential, especially when your data is traversing the internet and this is where VPNs come in. Using any VPN is not enough however, as picking the right solution is highly important too.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
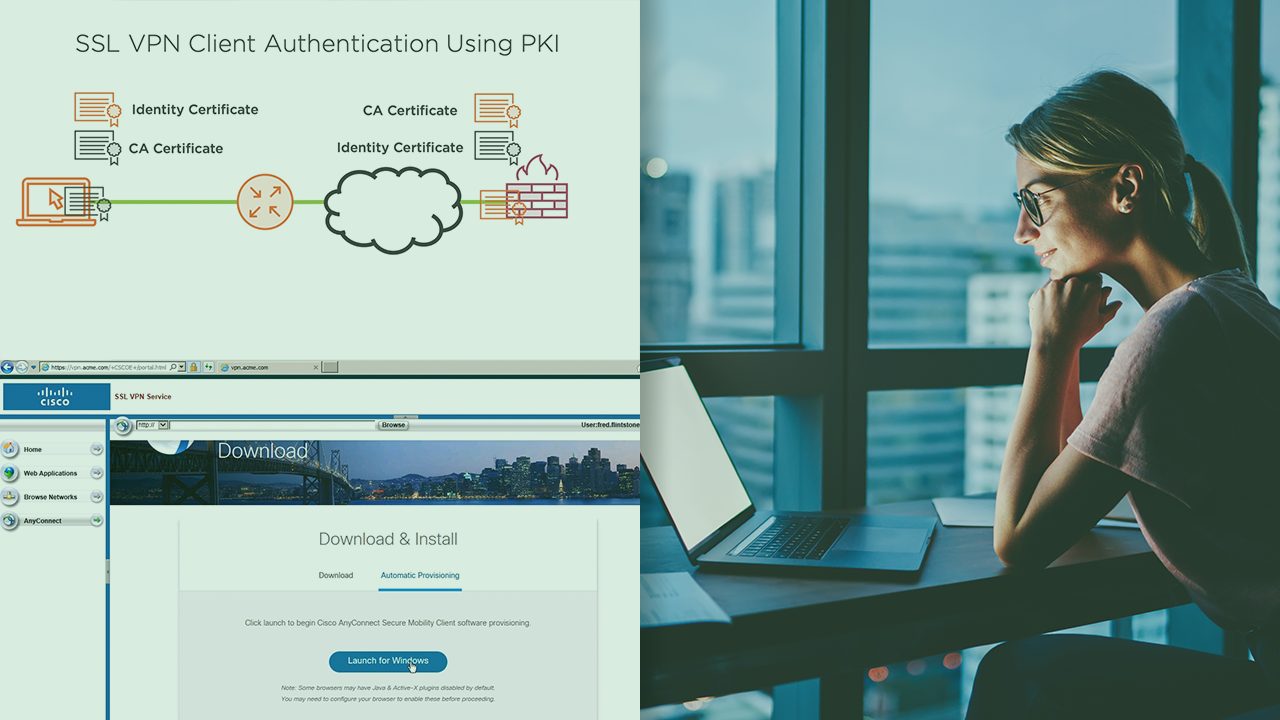
The value of data has increased substantially over the past few years with attackers capturing data or downloading it from compromised databases and selling it on the black market. Firewalls do their best to keep attackers out but what about protecting data that's being transmitted across an untrusted network such as the internet? This is exactly what VPNs were designed for. In this course, Architecting Cisco Secure Communications, you will not only learn about the different types of site-to-site and remote access VPNs available for organisations to use but you will also learn about the different components that come together to make up the different VPN solutions. First, you will explore site-to-site VPNs, starting with IPSec VPNs and moving onto GETVPNs and DMVPNs. Next, you will go through remote access VPNs including VPNs that can be accessed anywhere from any laptop or workstation without a client installed. Finally, you will learn how IPSec encryption keys are securely exchanged between VPN peers. When you are finished with this course, you will have the skills and knowledge of Cisco VPNs needed to determine the best VPN type of a given scenario.

