- Course
Authentication and Authorization in PHP
This course will teach you how to implement multiple methods of authentication and authorization in PHP.
- Course
Authentication and Authorization in PHP
This course will teach you how to implement multiple methods of authentication and authorization in PHP.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
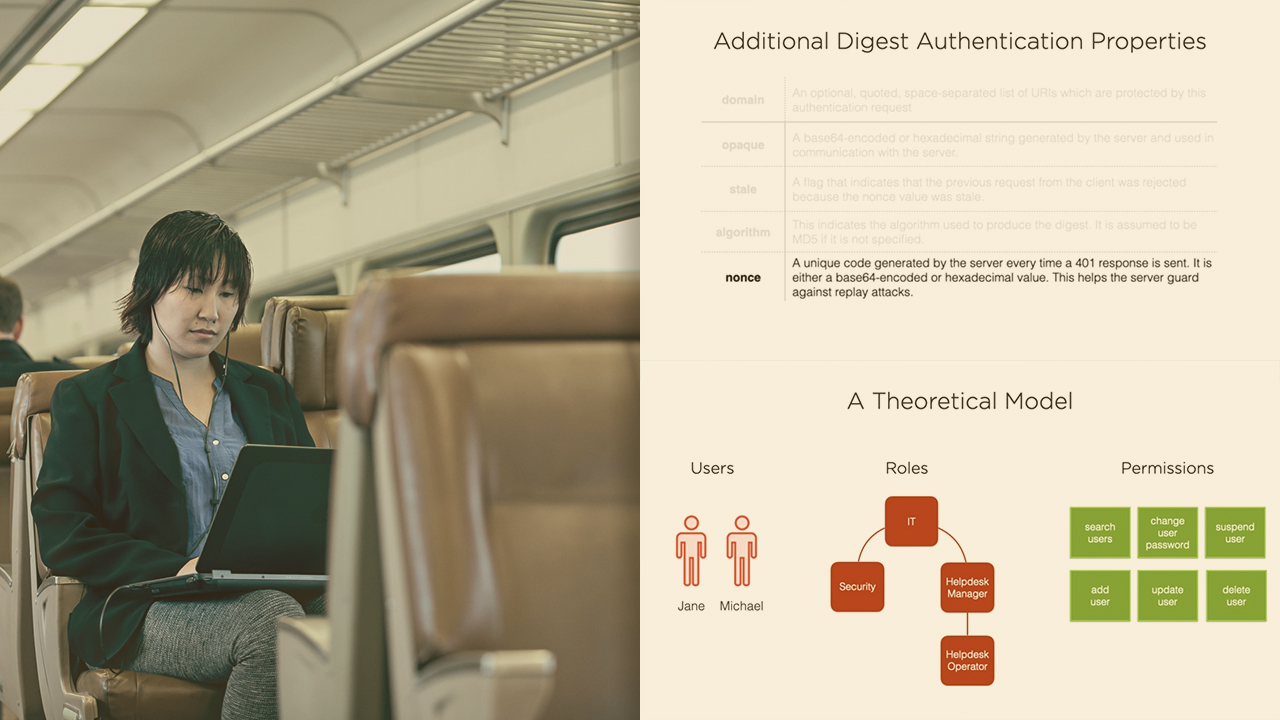
Implementing authentication and authorization in PHP are crucial for safeguarding your applications and ensuring proper usage of them. In this course, Authentication and Authorization in PHP, you’ll learn how to implement multiple methods of authentication and authorization using PHP. First, you'll explore how to implement four types of authentication: HTTP, Session, OAuth2, and OIDC. Next, you’ll discover how to implement two types of authorization: Role-based Access Control (RBAC) and Access Control Lists (ACLs). Finally, you'll get a broad introduction to modern privacy legislation and its impacts on the security measures which you implement in your applications. When you’re finished with this course, you’ll have the skills and knowledge needed to implement modern authentication and authorization in your PHP web applications.

