- Course
Auditing AWS Environments for Security and Best Practices
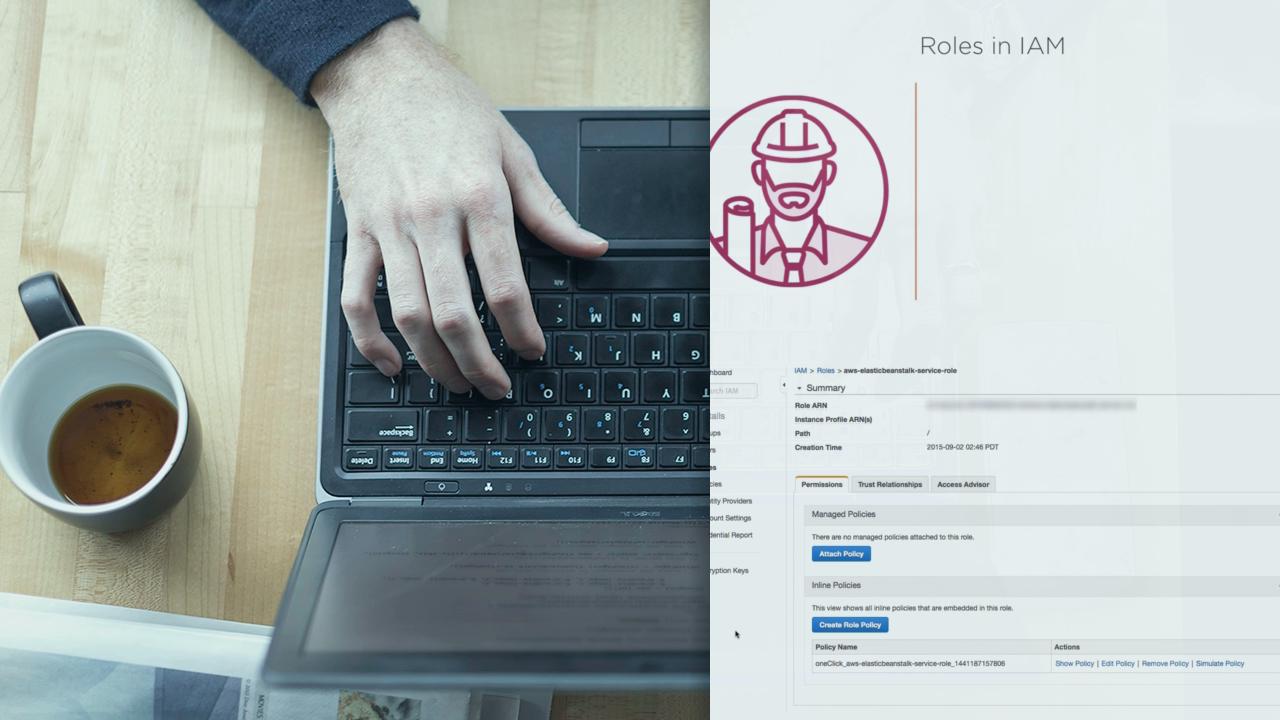
AWS is the most popular cloud hosting infrastructure in the world. This course will cover security and best practices for the most commonly used services, including IAM, VPC, EC2, EBS, and S3.
- Course
Auditing AWS Environments for Security and Best Practices
AWS is the most popular cloud hosting infrastructure in the world. This course will cover security and best practices for the most commonly used services, including IAM, VPC, EC2, EBS, and S3.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
What you'll learn
Taking ownership of an Amazon Web Services account can be a daunting task. In this course, Auditing AWS for Security and Best Practices, you'll learn how to audit your AWS services, including command-line tools and scripts to help automate your effort. First, you will learn how to look for security vulnerabilities. Next, you'll learn how to take an inventory of your resources. Finally, you'll learn about best practices for these services and how to apply them. When you're finished with this course, you will have learned the basics needed to implement security and architectural best practices in five of the most popular AWS offerings: IAM, VPC, EC2, EBS, and S3. Software required: AWS CLI

