- Course
Building and Implementing an Enterprise-level Phishing Program
The collective belief is that the "People" element is the weakest link in cyber defense. Leveraging this course can help you build your phishing program from scratch, implement it, select a suitable vendor, and optimize to the needs of your organization.
- Course
Building and Implementing an Enterprise-level Phishing Program
The collective belief is that the "People" element is the weakest link in cyber defense. Leveraging this course can help you build your phishing program from scratch, implement it, select a suitable vendor, and optimize to the needs of your organization.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
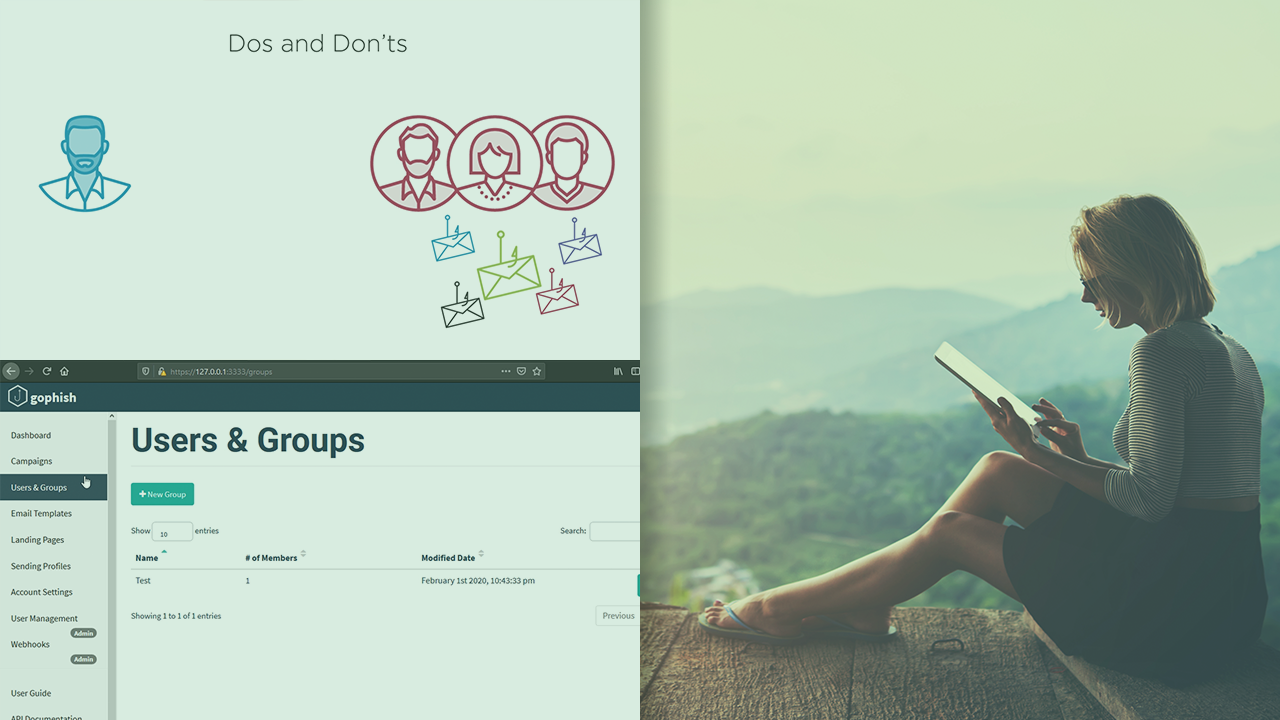
What you'll learn
Can you quantify the cyber risk posed by your employees to your organization? An Enterprise-level Phishing Program can tell you exactly which employee, which branch, region, or country of your firm is posing the maximum cybersecurity risk. In this course, Building and Implementing an Enterprise-level Phishing Program, you will gain the ability to effectively run an enterprise-level phishing program. First, you will learn to decide the scope and audience. Next, you will discover the basics of running the campaigns including designing the campaign, prioritizing the audience, selecting a third-party vendor, and running the campaigns. Finally, you will explore what metrics to track and how to effectively link the phishing program to other Infosec activities in your organization. When you’re finished with this course, you will have the know-how to effectively complement your Infosec training and awareness program with a well defined Phishing Simulation.

