- Course
CCSP®: Cloud Platform Security
Cloud Platform Security includes the essential elements of protection when consuming cloud services. Learn what these elements are, when to use them, and what they accomplish for your organization.
- Course
CCSP®: Cloud Platform Security
Cloud Platform Security includes the essential elements of protection when consuming cloud services. Learn what these elements are, when to use them, and what they accomplish for your organization.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
- Security
What you'll learn
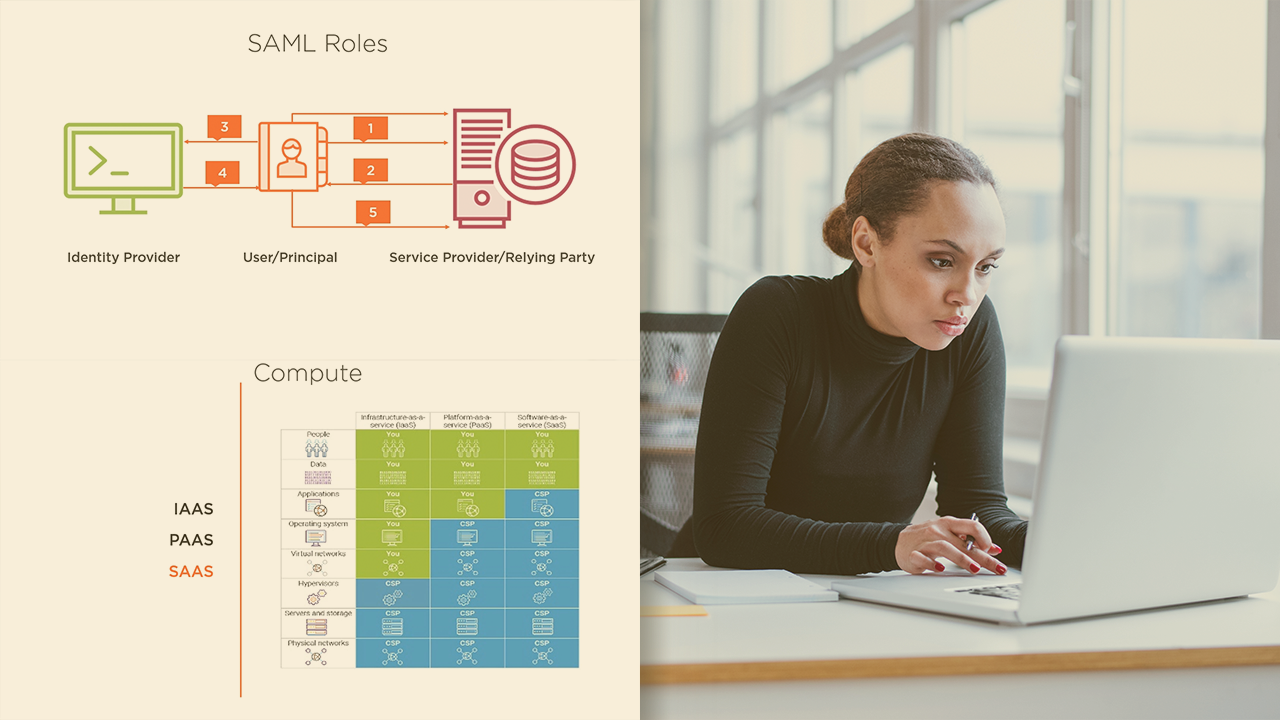
Cloud Platorm Security offers a new level of confidence for security and protection while using cloud services. In this course, CCSP: Cloud Platform Security, you will learn the steps to take to be better prepared to protect your organization's cloud platforms. First, you will look at how to enumerate the primary services of the cloud that will aid you in selection, advising, and managing your cloud environments. Next, you will discover what identity access management tools and protocols should be used given a business requirement. Finally, you will discover how to devise and execute on a list of controls that will aid you in protecting access to your services. By the end of this course, you will be better prepared to protect your cloud platform.

