- Course
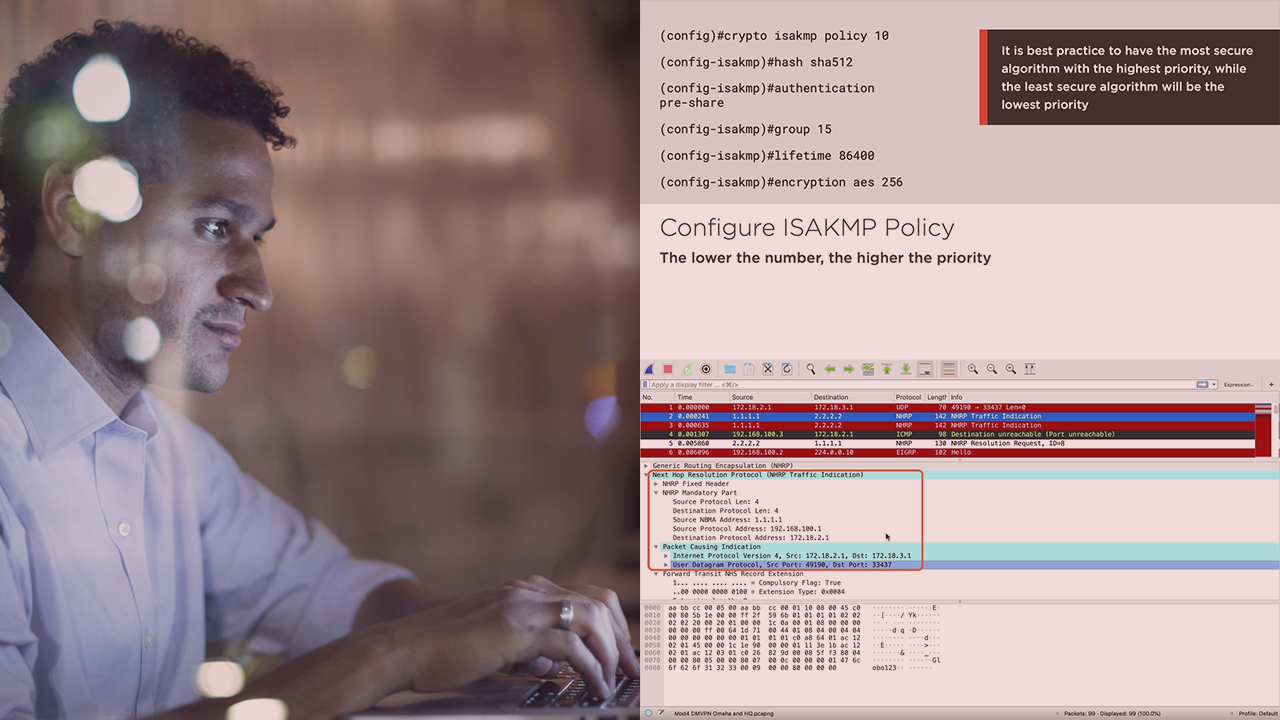
Cisco Core Security: Describing and Configuring VPNs
VPNs secure business traffic over the unprotected internet. Learn how to deploy either site-to-site VPNs using Cisco routers, or remote access VPNs using an ASA, or FTD.
- Course
Cisco Core Security: Describing and Configuring VPNs
VPNs secure business traffic over the unprotected internet. Learn how to deploy either site-to-site VPNs using Cisco routers, or remote access VPNs using an ASA, or FTD.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
The internet is an insecure way of transmitting confidential information, but dedicated circuits can be very expensive. In this course, Cisco Core Security: Describing and Configuring VPNs, you will gain the ability to understand and deploy various types of VPNs. First, you will learn about cryptography components, and how to configure cryptography on Cisco devices. Next, you will discover how to deploy various site-to-site VPNs using Cisco routers. Finally, you will explore how to configure a headend device to accept remote access VPNs using either Cisco’s Adaptive Security Appliance or Firepower Threat Defense. When you’re finished with this course, you will have the skills and knowledge of cryptography needed to deploy various types of VPNs.

