- Course
Collection with PowerSploit
After getting access to a few machines on the network, your next task in a red team engagement is collecting sensitive information. In this course, you will explore the PowerSploit tool, which is one of the main tools of a red team professional.
- Course
Collection with PowerSploit
After getting access to a few machines on the network, your next task in a red team engagement is collecting sensitive information. In this course, you will explore the PowerSploit tool, which is one of the main tools of a red team professional.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
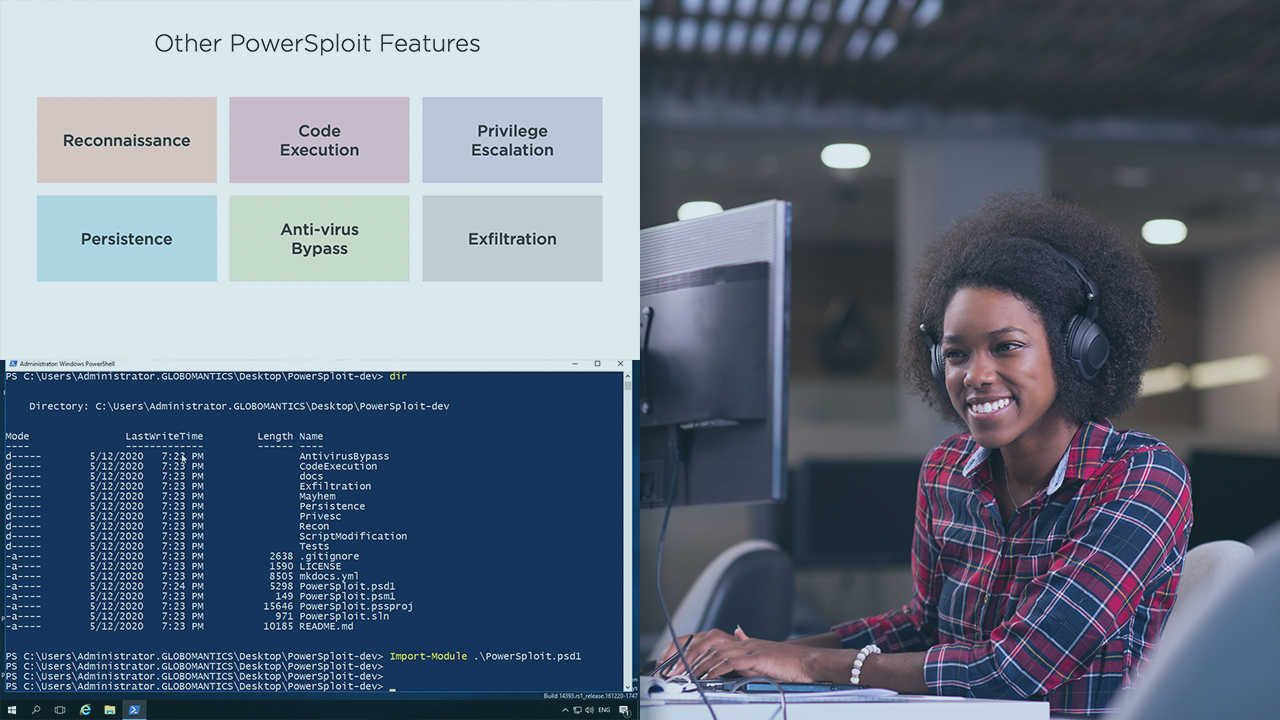
One of the main differences between a penetration testing and a red team engagement is executing the same attacks as malicious actors to demonstrate the impact a real attack to our clients. Therefore, after getting access to a few machines in the network, your job is to look for sensitive information that could be interesting for hackers. In this course, Collection with PowerSploit, you will cover one of the most important tools for a red team specialist, the PowerSploit framework. Here, you focus on the collection capabilities of this tool, which includes collecting keystrokes using a stealthy keylogger, collecting screenshots, collecting audio from the victim’s microphone, and even searching for sensitive files in the computers and network shared folders. This course covers four important tactics from the MITRE ATT&CK framework: Audio Capture (T1123), Input Capture (T1056), Screen Capture (T1113) and Data from Network Shared Drive (T1039).

