- Course
Cryptography and PKI for CompTIA Security+
Encryption is a vital component to every company's security posture and provides the means to securely access, transmit, verify, and dispose of data. In this course, you'll learn the fundamentals of cryptography and Public Key Infrastructure (PKI).
- Course
Cryptography and PKI for CompTIA Security+
Encryption is a vital component to every company's security posture and provides the means to securely access, transmit, verify, and dispose of data. In this course, you'll learn the fundamentals of cryptography and Public Key Infrastructure (PKI).
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
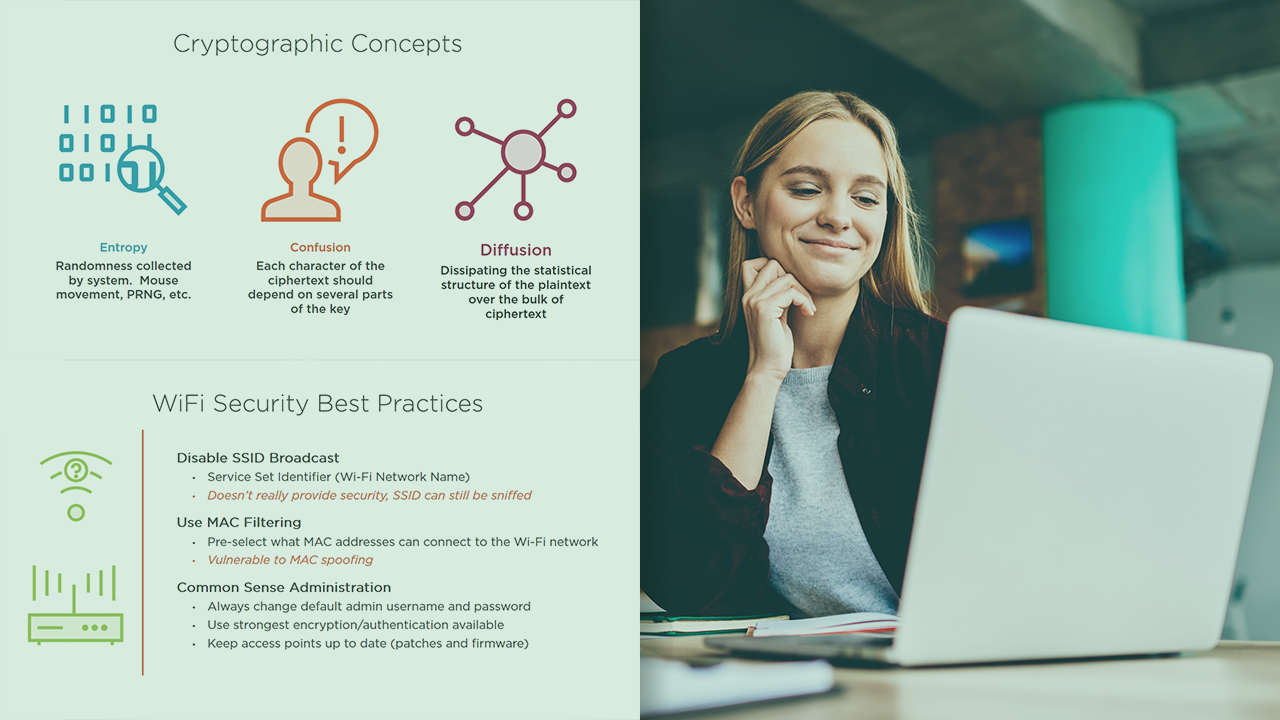
Providing secure communication, access to data, and disposal of assets is no longer essential to every company's overall IT security plan. In this course, Cryptography and PKI for CompTIA Security+, you'll learn the various concepts and components that make up a company's Public Key Infrastructure (PKI). First, you'll delve into the basics of cryptography, including symmetric and asymmetric algorithms, and cipher types. Next, you'll explore the various methods to encrypt data and how to verify a file's integrity. Then, you'll discover how to secure wireless communication using encryption. Finally, you'll learn about the components that make up a PKI. By the end of this course, you'll have the information necessary to discuss and assess your company's PKI, wireless security posture, and identify gaps both internally and externally.

