- Course
Container Infrastructure Analysis with Trivy
Want to learn how to find vulnerabilities in docker images? How about preventing these vulnerabilities in the first place? If so, you're in the right place! In this course you will learn Container Infrastructure Analysis with Trivy.
- Course
Container Infrastructure Analysis with Trivy
Want to learn how to find vulnerabilities in docker images? How about preventing these vulnerabilities in the first place? If so, you're in the right place! In this course you will learn Container Infrastructure Analysis with Trivy.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
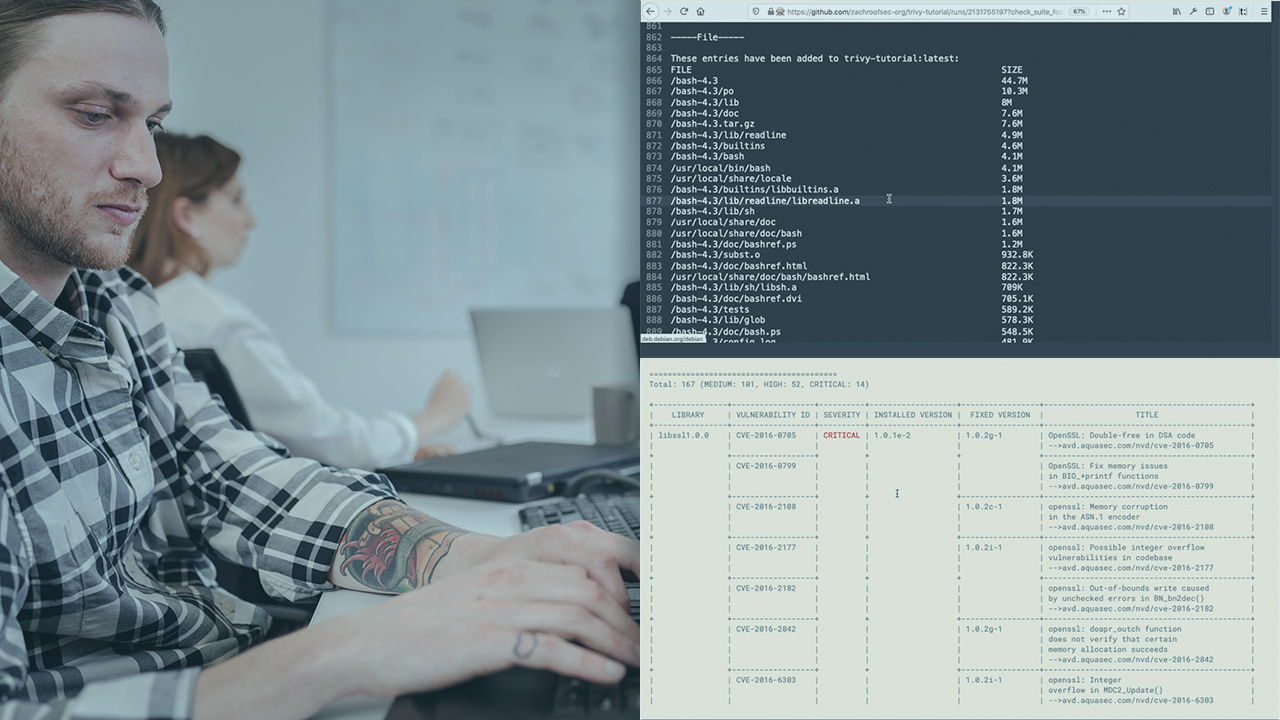
In this course, we will focus on automating docker image security scans. First, we will use Trivy (and a Github Action) to scan Dockerfiles within Github. Second, we will use Trivy to uncover a malicious image within a Docker registry. Third, we will perform an analysis on the malicious image to uncover the source of compromise. When you’re finished with this course, you’ll have the skills and knowledge to detect these techniques: Supply Chain Compromise (T1195), Implant Container Image (T1525).

