- Course
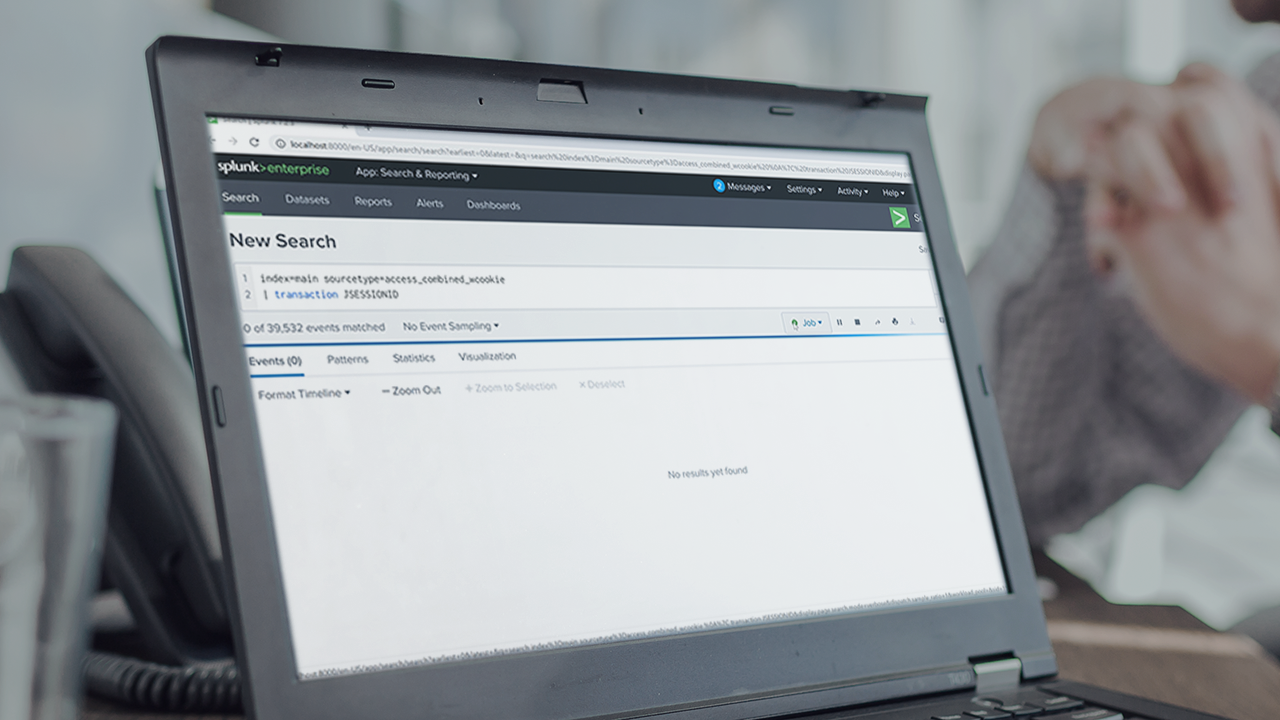
Correlating Events with Transactions in Splunk
You will master how to correlate and group events in Splunk using transactions. Through many examples, you will learn how to generate reports and dashboards, extract fields, and compare alternative approaches to transactions.
- Course
Correlating Events with Transactions in Splunk
You will master how to correlate and group events in Splunk using transactions. Through many examples, you will learn how to generate reports and dashboards, extract fields, and compare alternative approaches to transactions.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Correlating events in Splunk is an essential skill every Splunk user must have. Unfortunately, identifying and employing the right SPL commands with appropriate options can be very difficult. In this course, Correlating Events with Transactions in Splunk, you will gain a foundational knowledge of Correlating techniques in Splunk using transactions. First, you will learn the transaction command and all its useful options. Next, you will discover the all-powerful rex command to extract fields and use them in transactions. Then, you will explore how to generate reports and dashboards using transaction results. Finally, you will also gain an understanding of alternative commands such as stats and join, and when to use them. When you’re finished with this course, you will have the skills and knowledge of correlating and grouping events needed to effectively make sense of your machine data.

