- Course
Ethical Hacking: SQL Injection
Pluralsight is not an official partner or accredited training center of EC-Council. This course goes through how to detect SQL injection and identify risks as you to become an ethical hacker with a strong SQL injection understanding.
- Course
Ethical Hacking: SQL Injection
Pluralsight is not an official partner or accredited training center of EC-Council. This course goes through how to detect SQL injection and identify risks as you to become an ethical hacker with a strong SQL injection understanding.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
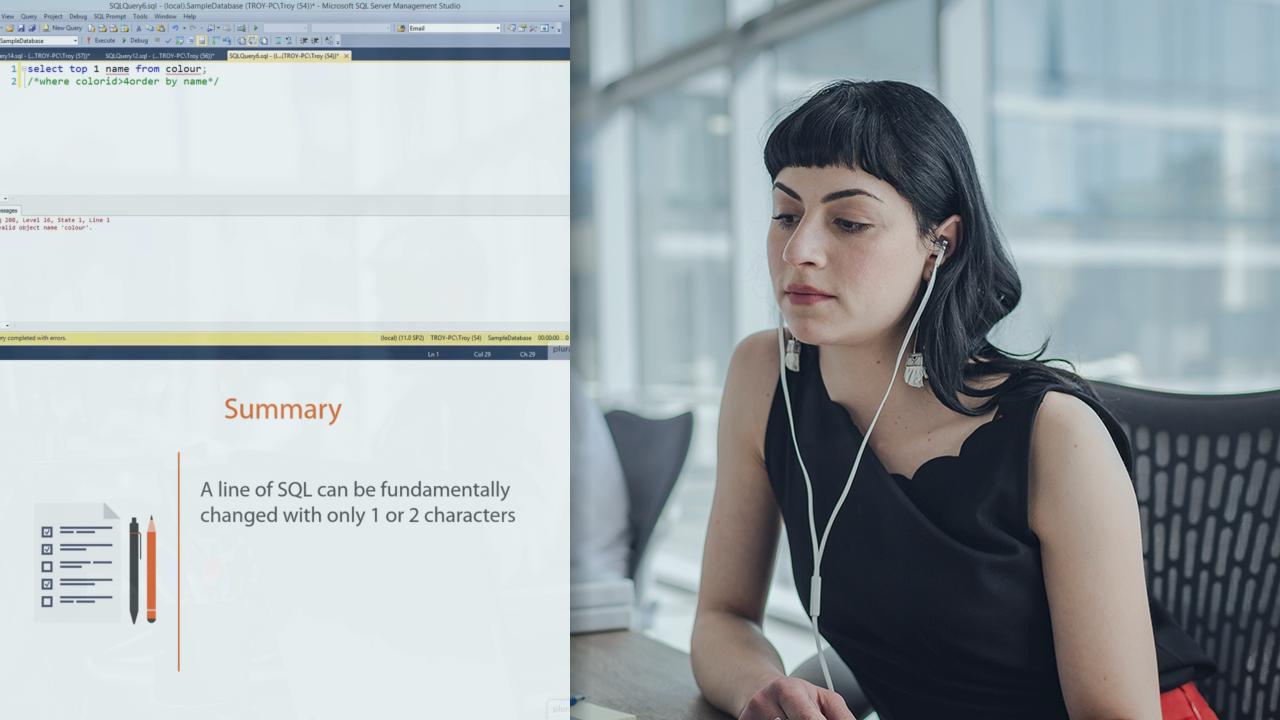
Pluralsight is not an official partner or accredited training center of EC-Council. Ever since we started connecting websites to databases, SQL injection has been a serious security risk with dire ramifications. The ability for attackers to run arbitrary queries against vulnerable systems can result in data exposure, modification, and in some cases, entire system compromise. SQL injection is classified as the number one risk on the web today due to the "perfect storm" of risk factors. It's very easily discoverable, very easily exploited, and the impact of a successful attack is severe. Add to that the fact that injection risks remain rampant, it's clear how it deserves that number one spot. This course takes you through everything from understanding the SQL syntax used by attackers, basic injection attacks, database discovery and data exfiltration, advanced concepts, and even using injection for network reconnaissance and running system commands. It's everything an ethical hacker needs to know to be effective in identifying the SQL injection risk in target systems. This course is part of the Ethical Hacking Series. http://blog.pluralsight.com/learning-path-ethical-hacking

