- Course
Getting Started with PowerSploit 1
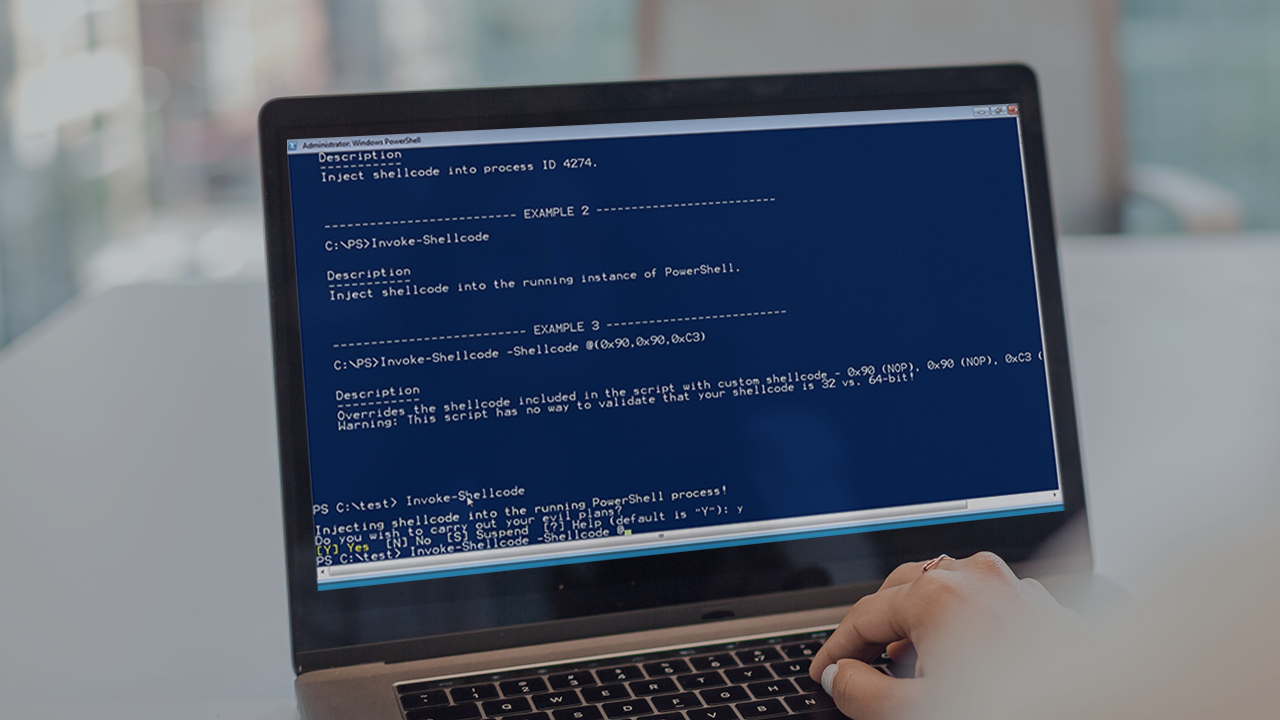
For years, the tools contained within PowerSploit have provided attackers and defenders with the capability to easily exploit misconfigured AD environments. Learn how to use PowerSploit to compromise systems, gather data, and escalate privileges.
- Course
Getting Started with PowerSploit 1
For years, the tools contained within PowerSploit have provided attackers and defenders with the capability to easily exploit misconfigured AD environments. Learn how to use PowerSploit to compromise systems, gather data, and escalate privileges.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
PowerSploit provides tools that assist defenders and attackers in identifying and exploiting vulnerabilities in Windows based networks and systems. In this course, Getting Started with PowerSploit 1, you will learn foundational knowledge to use the tools provided within the PowerSploit Post Exploitation Framework. First, you will learn how to leverage the tools within the code execution module. Next, you will discover how you can use PowerSploit to identify escalation opportunities. Finally, you will explore how to perform enumeration activities. When you're finished with this course, you will have the skills and knowledge of PowerSploit needed to incorporate PowerSploit into your testing activities.

