- Course
Infrastructure Security for CCNP Routing & Switching 300-115 SWITCH
Learn about SWITCH security features and how to use them to protect your network while preparing yourself for the CCNP SWITCH (300-115) exam. You'll cover DHCP snooping, dynamic ARP inspection, centralized authentication, and more.
- Course
Infrastructure Security for CCNP Routing & Switching 300-115 SWITCH
Learn about SWITCH security features and how to use them to protect your network while preparing yourself for the CCNP SWITCH (300-115) exam. You'll cover DHCP snooping, dynamic ARP inspection, centralized authentication, and more.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
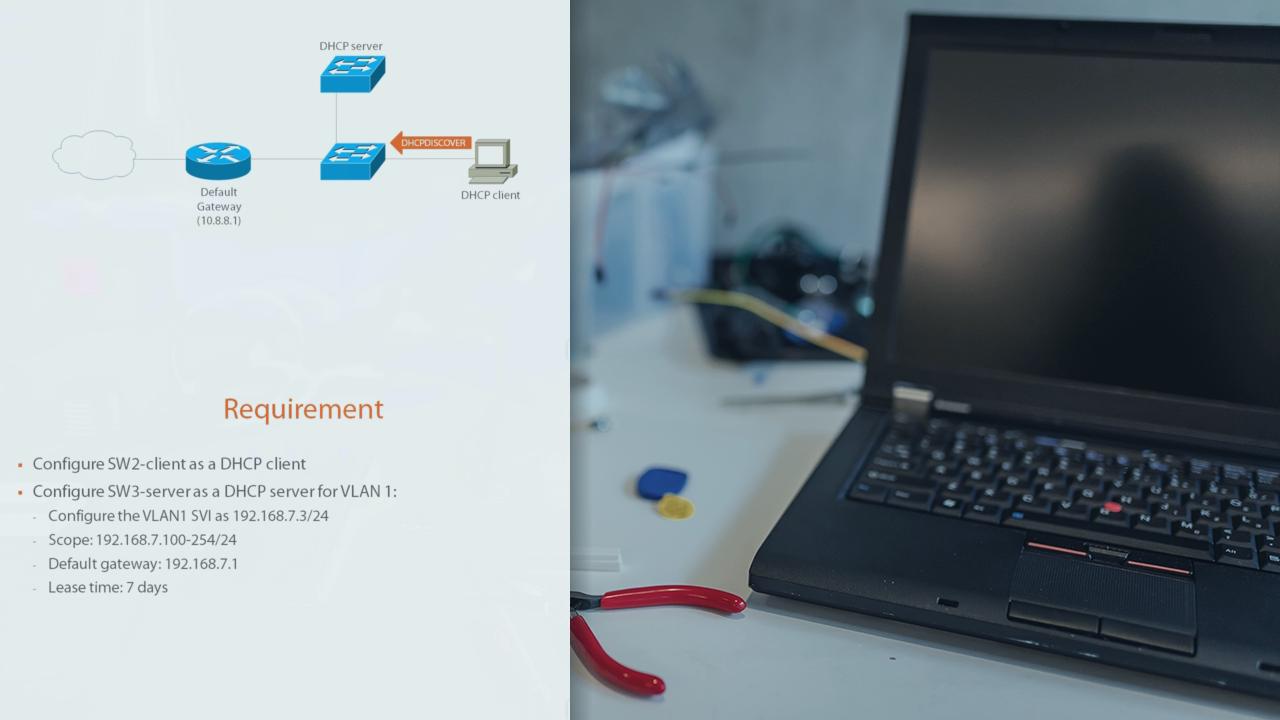
Learning how to properly secure the network infrastructure on your Cisco device can be overwhelming, but it doesn't have to be. This course, Infrastructure Security for CCNP Routing & Switching 300-115 SWITCH, will teach you the ins and outs in no time--it's also the final course on the CCNP SWITCH (300-115) exam. First, you'll cover SWITCH security features such as DHCP snooping and IP source guard and how they work together to protect your network from hackers. Next, you'll learn about how to use dynamic ARP inspection (DAI), port security, and storm control to keep hackers at bay. Finally, you'll learn about centralized authentication using RADIUS and TACACS+ and how to configure each of them, and end with a module that will help you prepare to succeed on your CCNP SWITCH exam. By the end of this course, you'll be able to secure your infrastructure, and you'll be one step closer to getting a great score on your 300-115 exam.

