- Course
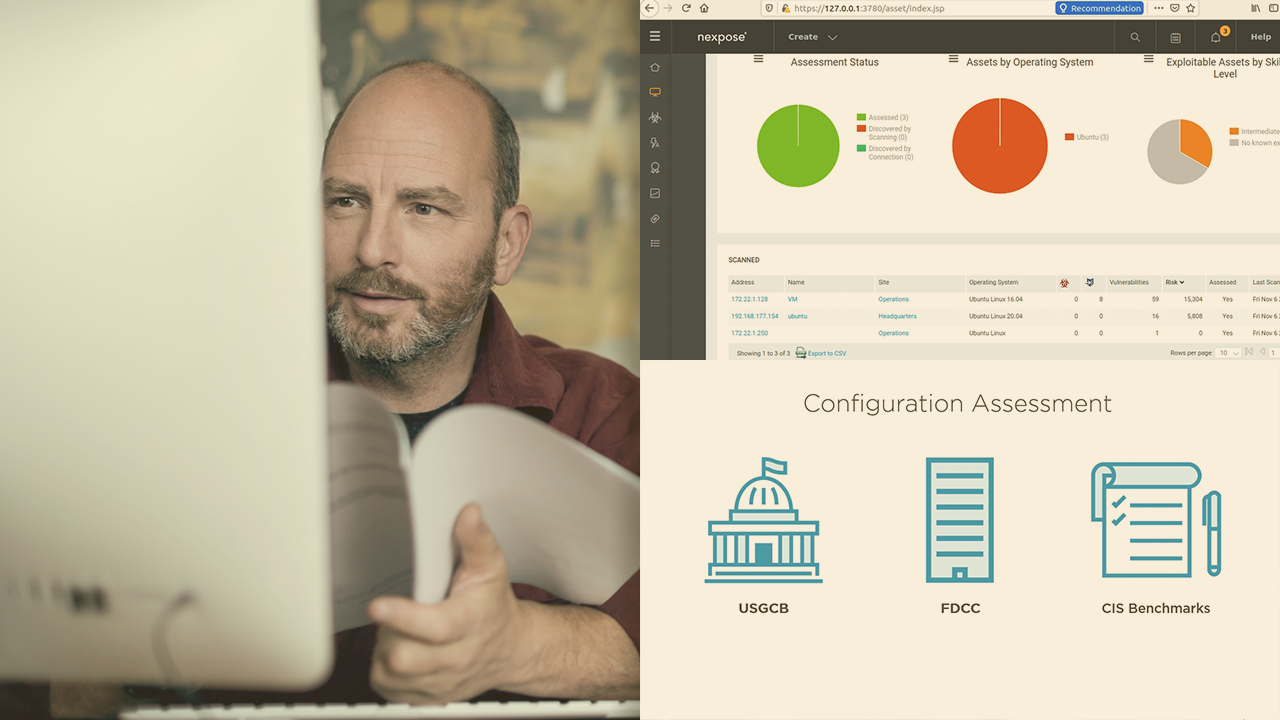
Investigate Network Targets with Nexpose
This course will teach you the best practices, methods, and procedures to use when deploying a large-scale enterprise scope vulnerability assessment using the Nexpose tool, plus learn how to strategize a plan for the effective investigation of targets.
- Course
Investigate Network Targets with Nexpose
This course will teach you the best practices, methods, and procedures to use when deploying a large-scale enterprise scope vulnerability assessment using the Nexpose tool, plus learn how to strategize a plan for the effective investigation of targets.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
All it takes is a review of the latest cybersecurity news and it is immediately clear that no matter what product or technology in use, there are still data breaches; therefore, the continued challenge is that of finding these weaknesses across the entire enterprise architecture. In this course, Investigate Network Targets with Nexpose, you’ll learn to create and test enterprise level vulnerability scans with the Nexpose Vulnerability Scanning Tool. First, you’ll explore and assess the large-scale deployment advanced scan configuration options. Next, you’ll discover and evaluate the different types of scan engines available within the Nexpose tool. Finally, you’ll learn how to prioritize and create custom scan schedules and efficiently leverage the advanced scanning characteristics and capabilities. When you’re finished with this course, you’ll have the skills and knowledge of how to Investigate Network Targets with Nexpose needed to scale to perform scans of large-scale enterprise networks.

