- Course
Microsoft Endpoint Manager: Device Configuration and Endpoint Protection with MECM
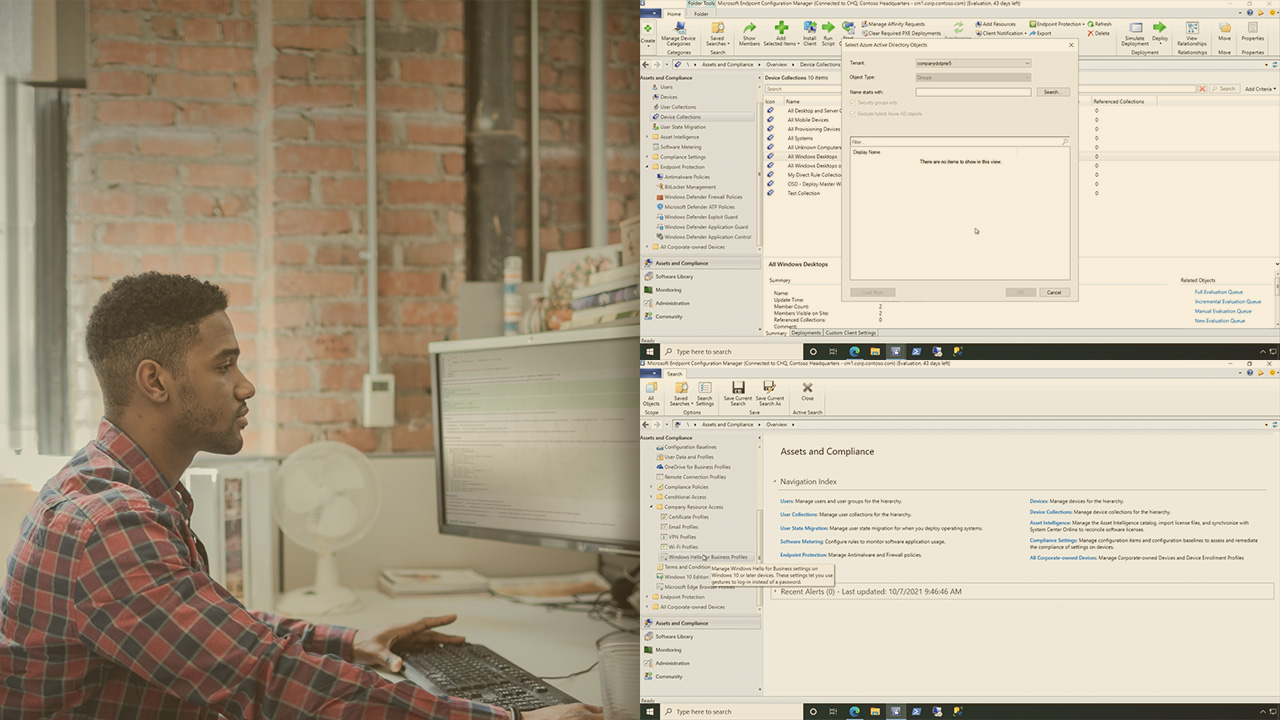
Understand the device configuration and endpoint protection features that you should -- and shouldn't -- implement via MECM in this course.
- Course
Microsoft Endpoint Manager: Device Configuration and Endpoint Protection with MECM
Understand the device configuration and endpoint protection features that you should -- and shouldn't -- implement via MECM in this course.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Although MECM has lived a longer lifecycle than Intune, along with that long history comes a few legacy approaches to performing certain tasks. This course on device configuration may seem a little strange, because significant portions of the course are all about tasks that you ... shouldn't ... do in Configuration Manager. For many of today's device configuration and endpoint protection activities, Microsoft Intune simply offers a far superior solution. That said though, understanding where these configurations exist in MECM, and which ones you should enable versus those you can safely ignore is the mission for this course.
In this eleventh course out of sixteen, Microsoft Endpoint Manager: Device Configuration and Endpoint Protection with MECM, you'll start by exploring the options in MECM that exist for deploying device configurations to clients. Some of these, perhaps not surprisingly, involve technologies that have nothing to do with MECM at all, while others involve approaches that are better served through Intune's more MDM-like architecture. Next, you'll look at the endpoint protection policies in MECM, including which ones remain relevant for configuring via MECM today versus those better delivered from the Azure cloud.

