- Course
Network Analysis with Arkime
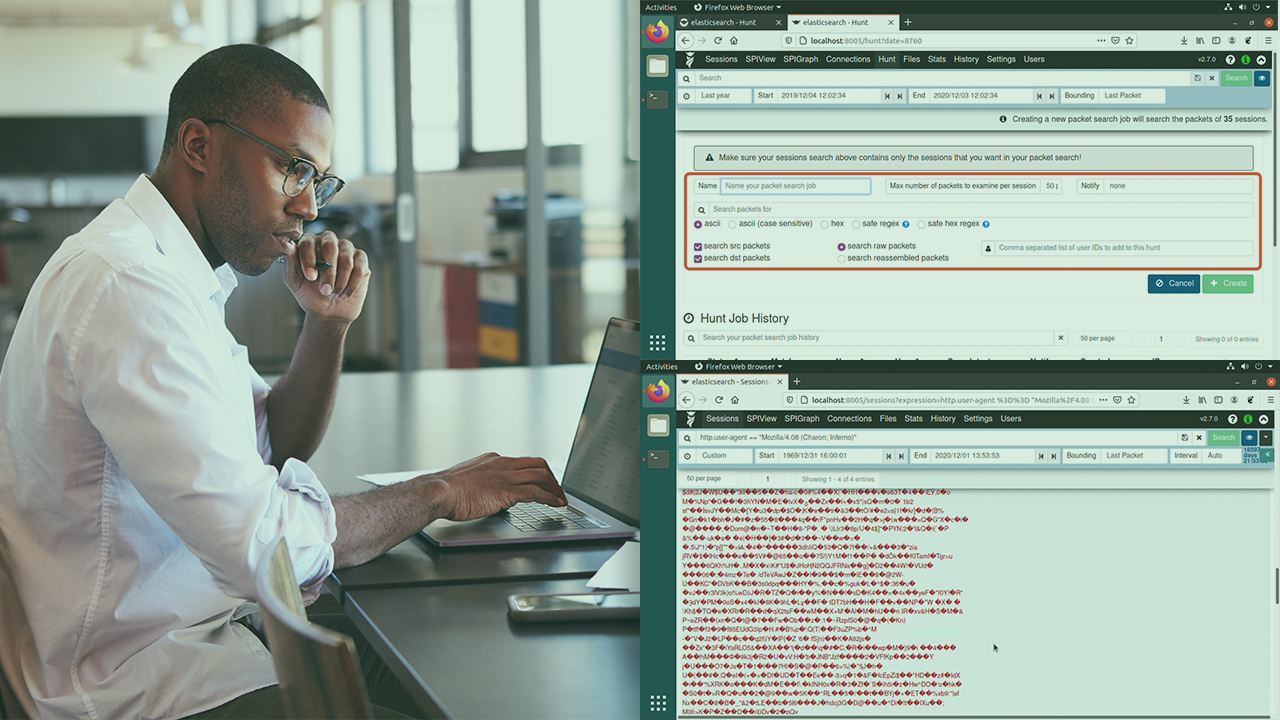
Analyzing network traffic is an important step in developing a proactive threat hunting program. This course will teach you how to perform network traffic analysis using Arkime to find threats in your network.
- Course
Network Analysis with Arkime
Analyzing network traffic is an important step in developing a proactive threat hunting program. This course will teach you how to perform network traffic analysis using Arkime to find threats in your network.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Finding undetected threats in your network through proactive network analysis requires the right tools. In this course, Network Analysis with Arkime, you’ll learn how to utilize Arkime to detect anomalous or malicious network traffic in an enterprise environment. First, you'll gain insight into how to detect common malware delivery patterns. Next, you’ll learn how to use Arkime to identify malware command and control. Finally, you’ll utilize the many features of Arkime to identify data exfiltration. When you’re finished with this course, you’ll have the skills and knowledge to detect these techniques using Arkime.

