- Course
Network Vulnerability Scanning with OpenVAS
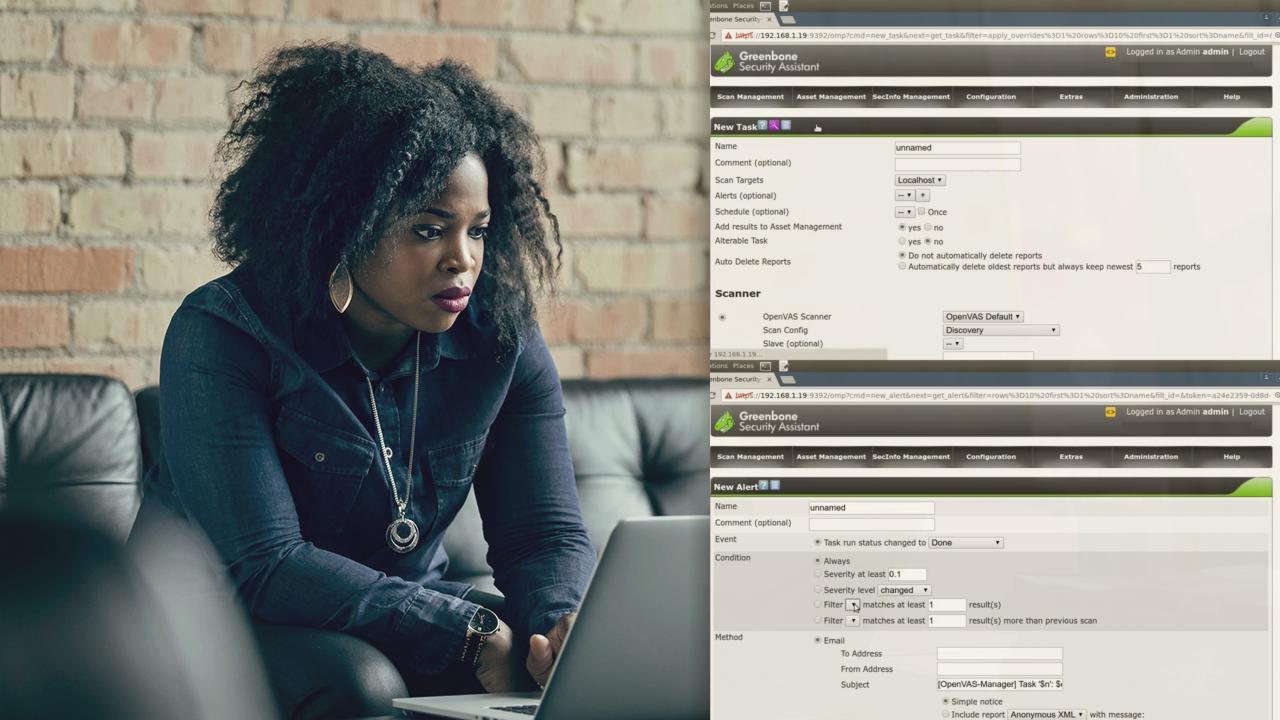
Before launching a penetration testing session, you must first assess the target network and its compute resources for known vulnerabilities. The OpenVAS suite is built to perform complete and effective vulnerability scans. Learn how it's done.
- Course
Network Vulnerability Scanning with OpenVAS
Before launching a penetration testing session, you must first assess the target network and its compute resources for known vulnerabilities. The OpenVAS suite is built to perform complete and effective vulnerability scans. Learn how it's done.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
All the penetration testing in the world won't amount to much if the software and routing configurations used in your infrastructure are buggy. But scanning systems for the tens of thousands of known vulnerabilities - and the dozens more that surface each week - would be simply impossible...without help. The OpenVAS vulnerability assessment suite brings together an actively curated database of vulnerabilities with powerful network scan and reporting tools. When properly set up, OpenVAS can largely automate the task of scanning for holes and, if desired, alert you only when there's something big. In this course, Network Vulnerability Scanning with OpenVAS, you will install and configure OpenVAS on Kali Linux (or any other Linux distribution). Next, you'll come to understand the roles played by each of the public vulnerability databases on which vulnerability scanning rely. Finally, you'll launch a range of scans against live targets, and make sense of the reports that your scans will generate. By the end of this course, you'll feel confident in adding this powerful open source tool to your toolbox.

