- Course
OS Analysis with The Sleuth Kit & Autopsy
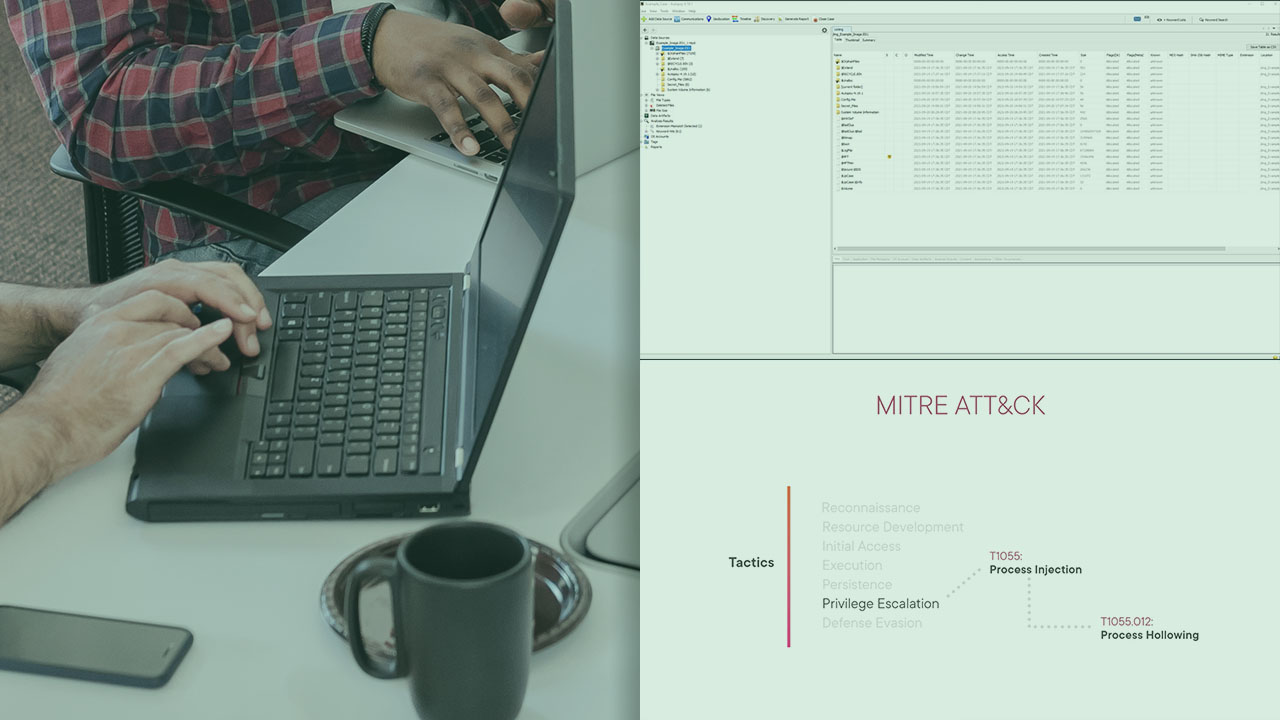
In this course you will learn how to parse file systems and extract forensic artifacts that can be invaluable to incident responders, security analysts, and threat hunters.
- Course
OS Analysis with The Sleuth Kit & Autopsy
In this course you will learn how to parse file systems and extract forensic artifacts that can be invaluable to incident responders, security analysts, and threat hunters.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Being able to effectively analyze digital evidence and extract indicators of compromise is incredibly important. In fact, it’s crucial to properly scoping an incident and creating robust detection logic to prevent and detect future attacks. In this course, OS Analysis with The Sleuth Kit & Autopsy, you’ll cover how to utilize Sleuth Kit and Autopsy to detect process injection and artifact obfuscation in an enterprise environment. First, you’ll demonstrate how to detect process injection techniques such as process hollowing and injection. Next, you’ll operate identifying and detecting artifact obfuscation. When you’re finished with this course, you’ll have the skills and knowledge to detect these techniques, Process Inject (T1055) and Artifact Obfuscation (T1027) using Sleuth Kit and Autopsy.

