- Course
OS Analysis with Wazuh 4
Want to learn how to detect process-level and file-level attacks? How about automatically blocking data exfiltration over a C2 channel? If so, you're in the right place! In this course you will learn OS Analysis using Wazuh.
- Course
OS Analysis with Wazuh 4
Want to learn how to detect process-level and file-level attacks? How about automatically blocking data exfiltration over a C2 channel? If so, you're in the right place! In this course you will learn OS Analysis using Wazuh.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
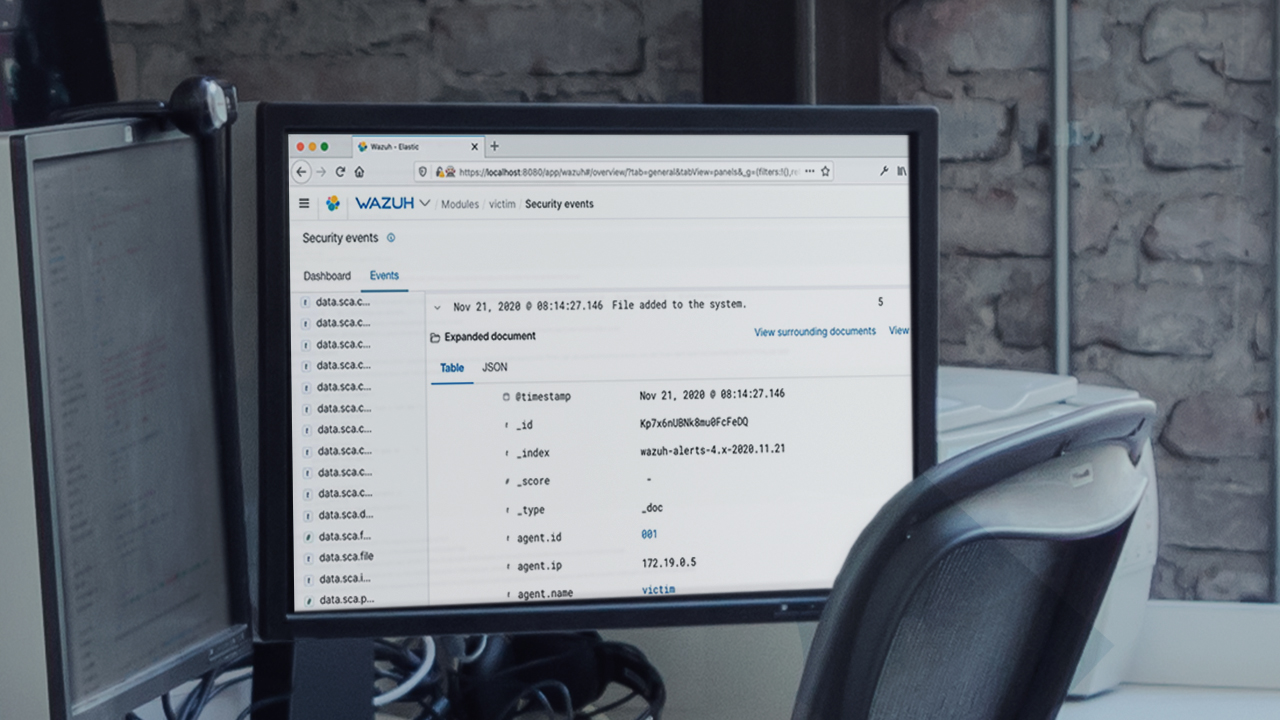
Detecting process-level and file-level attacks can be challenging. Additionally, many tools are "alert factories" that don't have the ability to remediate in-progress attacks. Luckily, Wazuh solves these problems! In this course, OS Analysis with Wazuh, you'll cover how to utilize Wazuh to respond to data exfiltration in an enterprise environment. First, you'll create a rule to detect malicious filesystem operations. Next, you'll uncover a rootkit through Wazuh by using a Python script. Finally, you'll leverage Wazuh's Active Response functionality to automatically quarantine the host (and prevent it from exfiltrating data). In this course, you will simulate all attacks through Merlin (a popular C2 service) so we can emulate real-world scenarios! (No prior Merlin experience is needed). When you're finished with this course, you'll have the skills and knowledge to detect these techniques: Scheduled Task/Job (T1053), Hijack Execution Flow (T1574), and Exfiltration Over C2 Channel (T1041).

