- Course
Penetration Testing Automation Using Python and Kali Linux
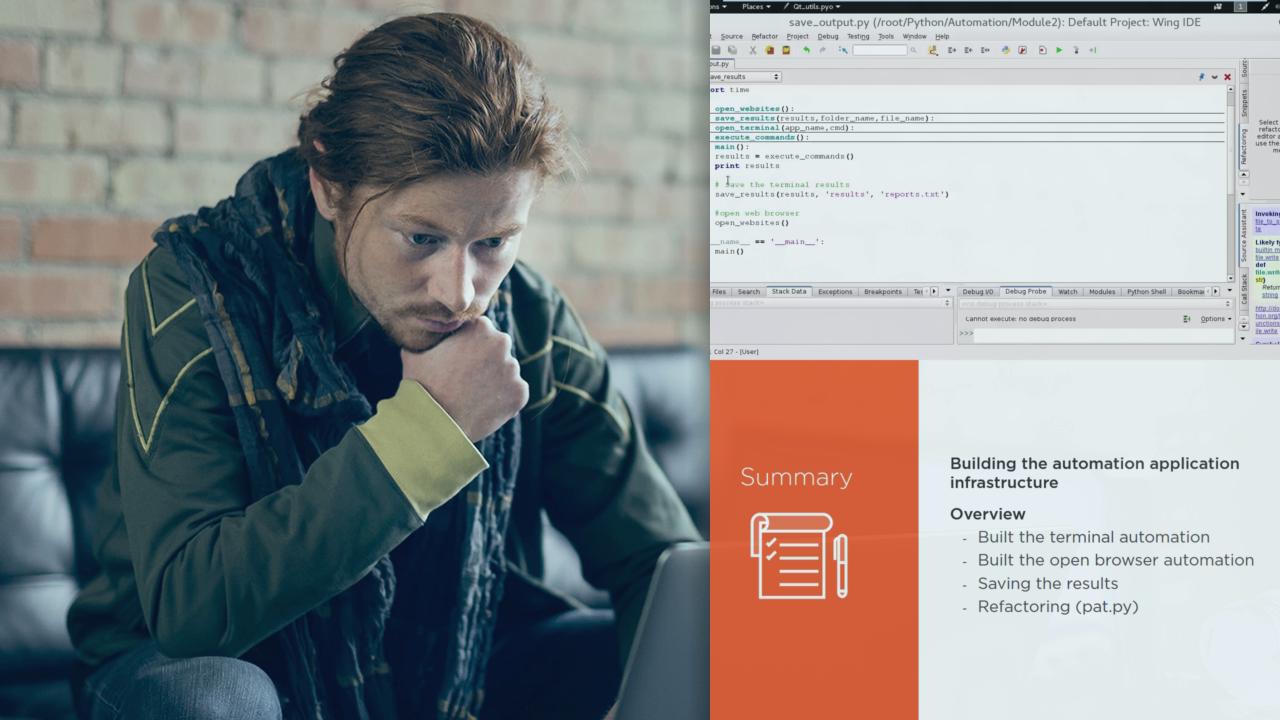
Learn how to build your own automated penetration testing application using Python and Kali Linux. Also, learn how to understand software tools and how they work.
- Course
Penetration Testing Automation Using Python and Kali Linux
Learn how to build your own automated penetration testing application using Python and Kali Linux. Also, learn how to understand software tools and how they work.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Get a good understanding on how to use Python to automate your web penetration testing scenarios. In this course, Penetration Testing Automation Using Python and Kali Linux, you'll learn how to start automating your penetration testing tasks using Python and Kali Linux. First, you'll learn about information gathering automation. Next, you'll learn about network scanning automation. Finally, you'll learn about vulnerabilities assessment automation. By the end of this course, you'll be able to develop your own automated scanner for gathering information, scanning the network, and conducting an automated vulnerability assessment.

