- Course
Post Exploitation: Performing Infrastructure Analysis
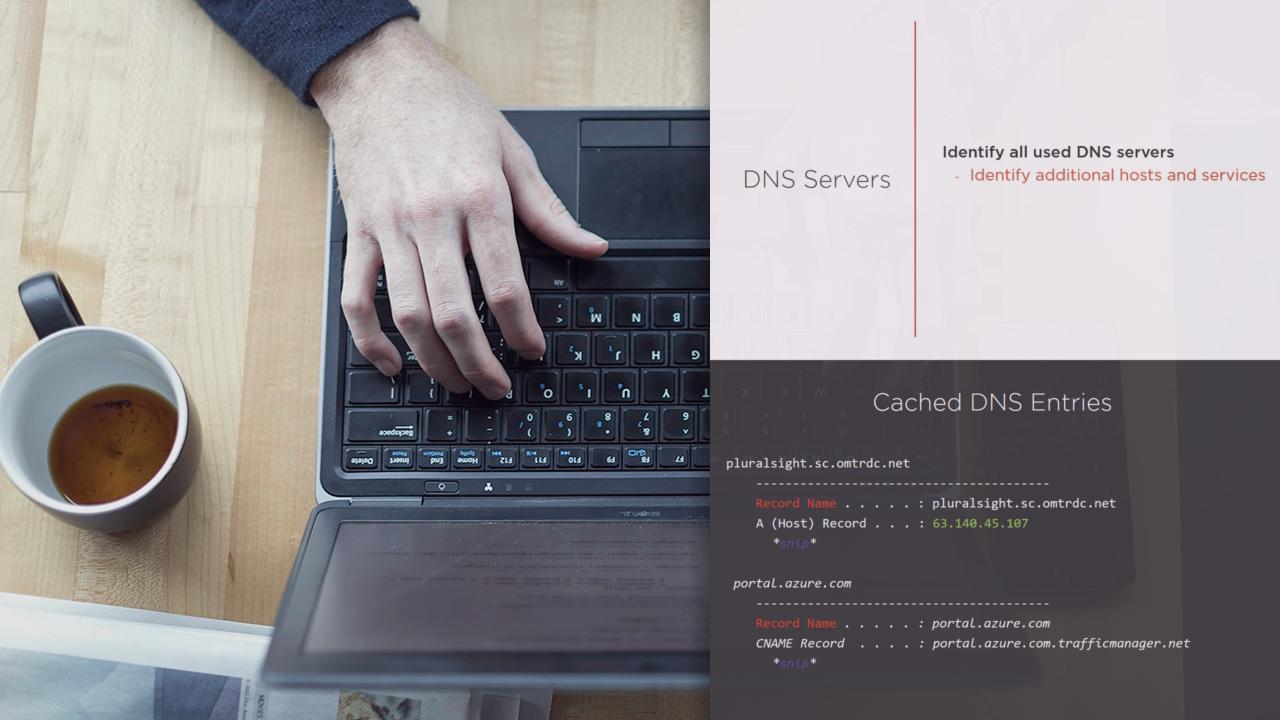
Everything that comes after the shell during a penetration test is called post exploitation. This course introduces post exploitation and performing infrastructure analysis through service and configuration enumeration in a compromised network.
- Course
Post Exploitation: Performing Infrastructure Analysis
Everything that comes after the shell during a penetration test is called post exploitation. This course introduces post exploitation and performing infrastructure analysis through service and configuration enumeration in a compromised network.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
When engaged in a penetration test for a client, after you successfully breach the perimeter, you may find yourself asking 'What next?' What are the steps that you need to perform before you can close the penetration test? In this course, Post Exploitation: Performing Infrastructure Analysis, you'll learn how to gather information pertaining to the network configuration and network services using both inbuilt as well as custom tools. Next, you'll also learn the best practices to follow while in an engagement. Additionally, you'll learn how to identify all the services that the compromised host is running in order to utilize and exploit later while attempting to extract data from the host. When you're finished with this course, you'll have the knowledge to gather information about infrastructure from the whole network, but most importantly, you'll learn how to use this information for a variety of purposes ranging from data exfiltration to privilege escalation.

