- Course
Protocol Deep Dive: IPsec
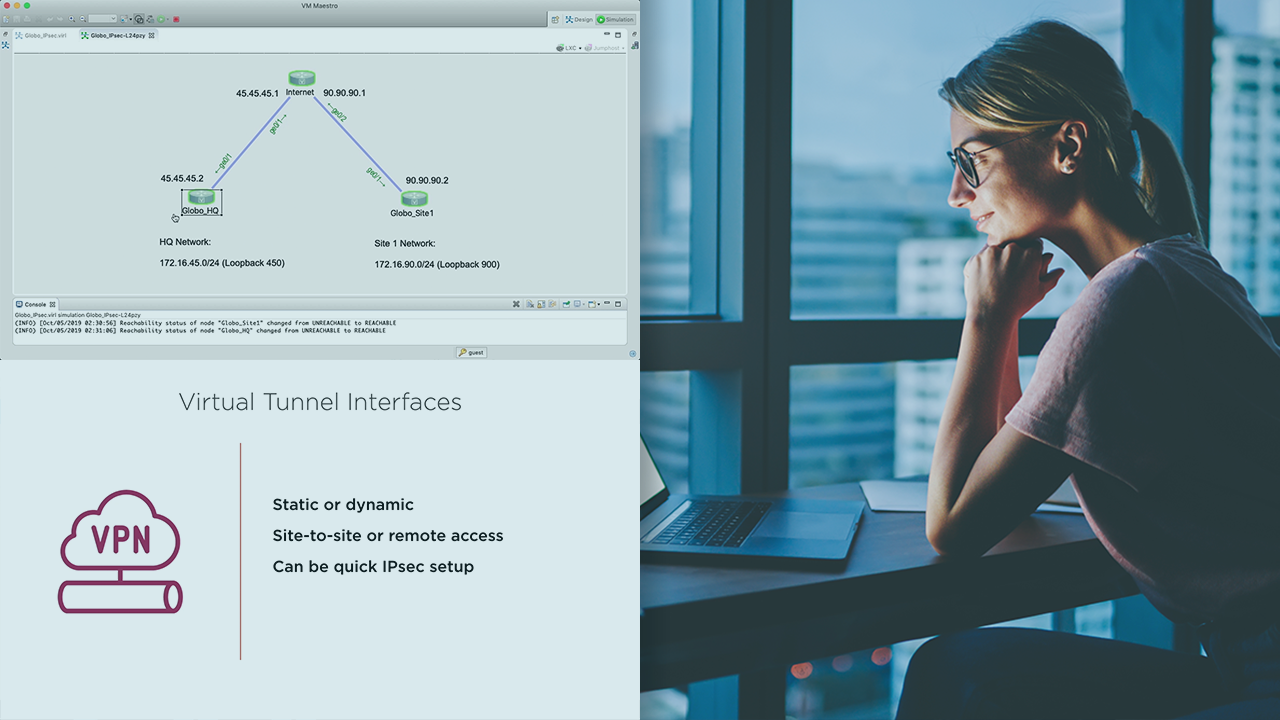
IPsec helps us to secure our infrastructure and offer services securely to our organization. This course will teach you how to configure, verify, and analyze IPsec, as well as teach you knowledge to give you a deep understanding of the technologies.
- Course
Protocol Deep Dive: IPsec
IPsec helps us to secure our infrastructure and offer services securely to our organization. This course will teach you how to configure, verify, and analyze IPsec, as well as teach you knowledge to give you a deep understanding of the technologies.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
IPsec is used in our environments and on our endpoints to secure our traffic. It enables us to transmit our information securely across unsecured connections. Learning how to configure, verify, and analyze IPsec in your environments will help you improve your organization's security posture. In this course, Protocol Deep Dive: IPsec, you will gain the skills necessary to use this technology and have a deep understanding of the protocol suite. First, you will learn all about the underlying protocols that make up IPsec and how they work together to make it work. Next, you will discover IKE and the role that it plays in the IPsec suite. Finally, you will explore IKEv1 and IKEv2, and see the differences between them so you can fully understand how and why you should implement them. When you're finished with this course, you will have a full understanding of the protocol suite and be able to utilize it effectively in many different ways and implementation methods.

