- Course
Incident Detection and Investigation with QRadar 7
In this course, you will explore the IBM Security QRadar SIEM tool from an SOC analyst perspective. This course is aligned to the "IBM QRadar SIEM V7.3.2 Fundamental Analysis" exam objectives (Exam C1000-018) with coverage of additional topics.
- Course
Incident Detection and Investigation with QRadar 7
In this course, you will explore the IBM Security QRadar SIEM tool from an SOC analyst perspective. This course is aligned to the "IBM QRadar SIEM V7.3.2 Fundamental Analysis" exam objectives (Exam C1000-018) with coverage of additional topics.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
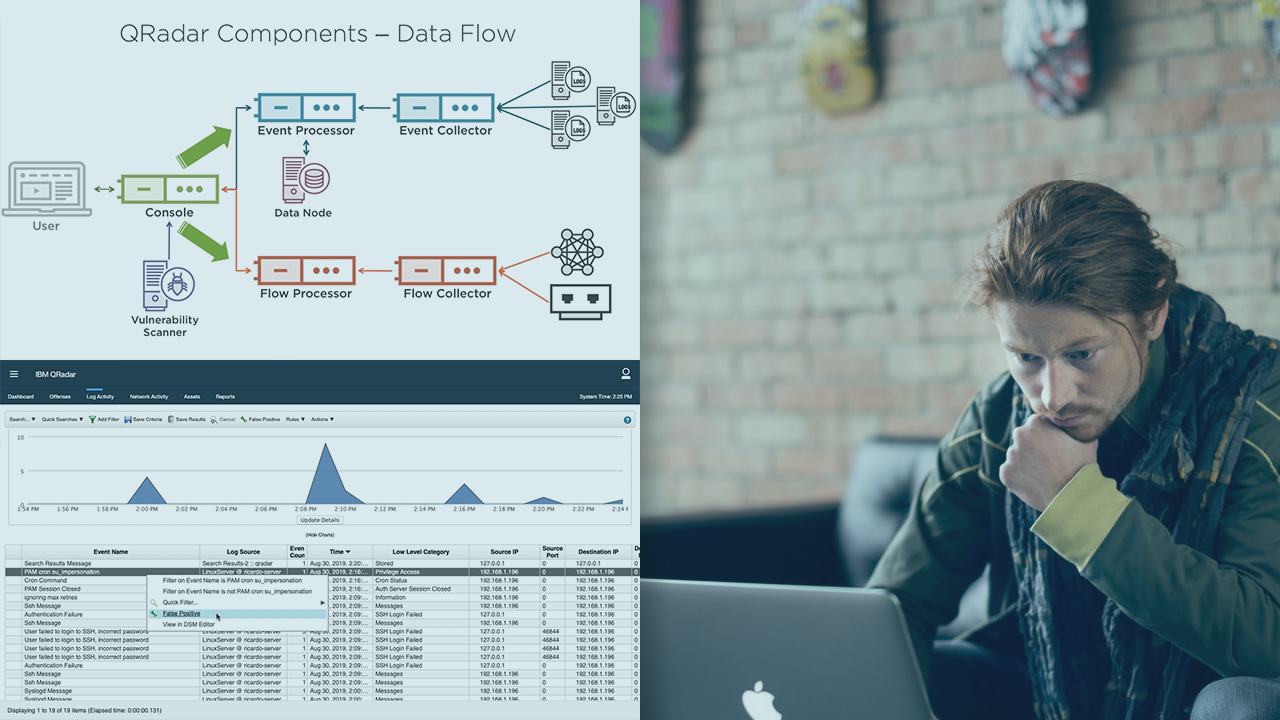
IBM Security QRadar is a leader in SIEM solutions according to the 2016 Gartner Magic Quadrant. In this course, Incident Detection and Investigation with QRadar, you will explore QRadar’s main features from an SOC analyst perspective. First, you will explore what SIEM is and how QRadar provides more functions than a regular SIEM. Next, you will walk through all relevant functionality provided by the tool and some extra functions, such as Risk Manager and Vulnerability Manager. Finally, with the SIEM basics covered, you will dive into incident investigation using QRadar, where you will learn about events, flows, and offenses. When you’ve completed this course, you’ll understand how to investigate the most common cyber threats using QRadar. This course covers the objectives of the "IBM QRadar SIEM V7.3.2 Fundamental Analysis" exam (Exam C1000-018) which is required to achieve the "IBM Certified Associate Analyst - IBM QRadar SIEM V7.3.2" certification.

