- Course
Implementing and Performing Risk Management with ISACA’s Risk IT Framework
Managing risk is a highly critical skill in today's organizations. This course will demonstrate the advanced skills you need to prepare your organization to effectively manage risk using the ISACA Risk IT Framework.
- Course
Implementing and Performing Risk Management with ISACA’s Risk IT Framework
Managing risk is a highly critical skill in today's organizations. This course will demonstrate the advanced skills you need to prepare your organization to effectively manage risk using the ISACA Risk IT Framework.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
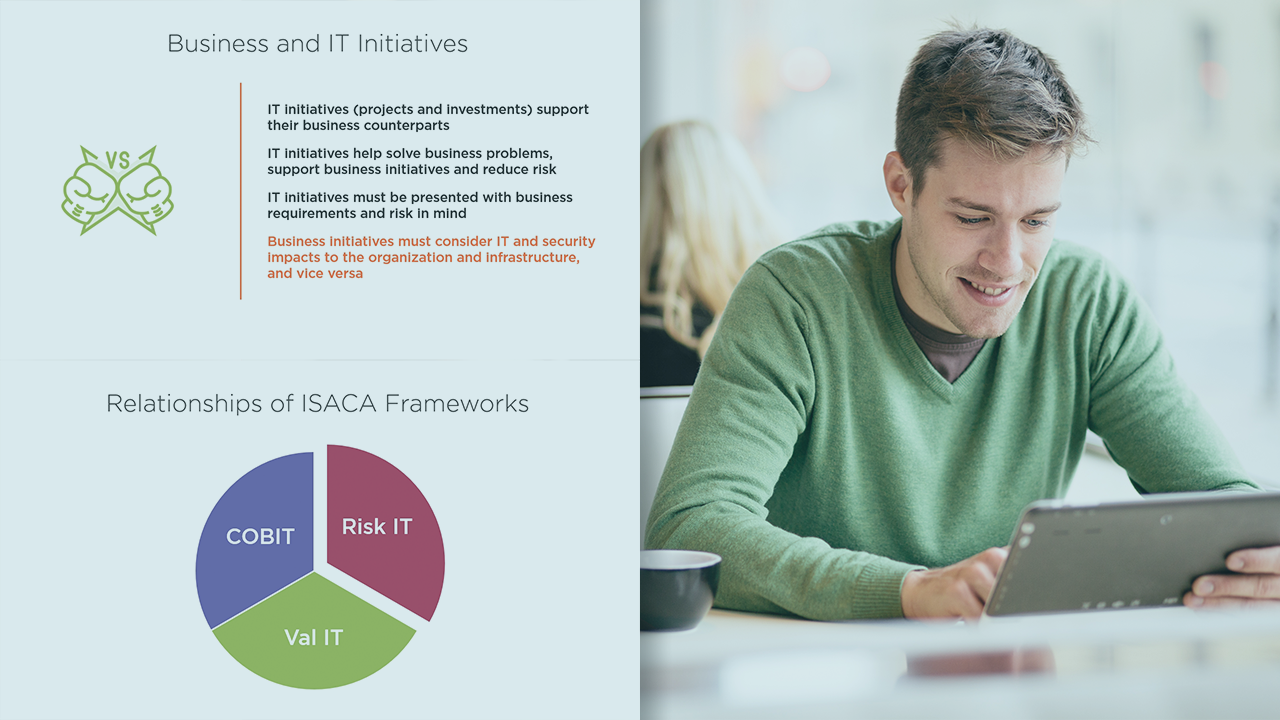
In today’s IT networks, risk is a critical element in balancing the ever-increasing threat of data breaches, lack of resources, and the need to ensure that IT supports business functions. Add complex compliance requirements from today’s regulatory environment, and the need for IT risk management is both obvious and urgent. Managing this risk focuses on three critical processes in the organization: governance, risk evaluation and analysis, and risk response. Organizations must have a solid framework in place to guide their cyber risk management efforts. In this course, Implementing and Performing Risk Management with ISACA’s Risk IT Framework, you'll gain your key to getting the practical knowledge you need to have to implement that framework. First, you’ll learn what the ISACA Risk IT Framework is and how it can be used to manage risk in your organization. Next, you’ll also learn how the Risk IT Framework articulates with COBIT and Val IT. This course will also show you how to implement the three domains of the framework, including Governance, Evaluation, and Response. Finally, you’ll learn how to implement and integrate the Risk IT Framework into your organization’s risk management strategy and processes. By the end of this course, you’ll have the advanced knowledge you need to help you manage the cyber risk program in your organization.

