- Course
Security Event Triage: Statistical Baselining with SIEM Data Integration
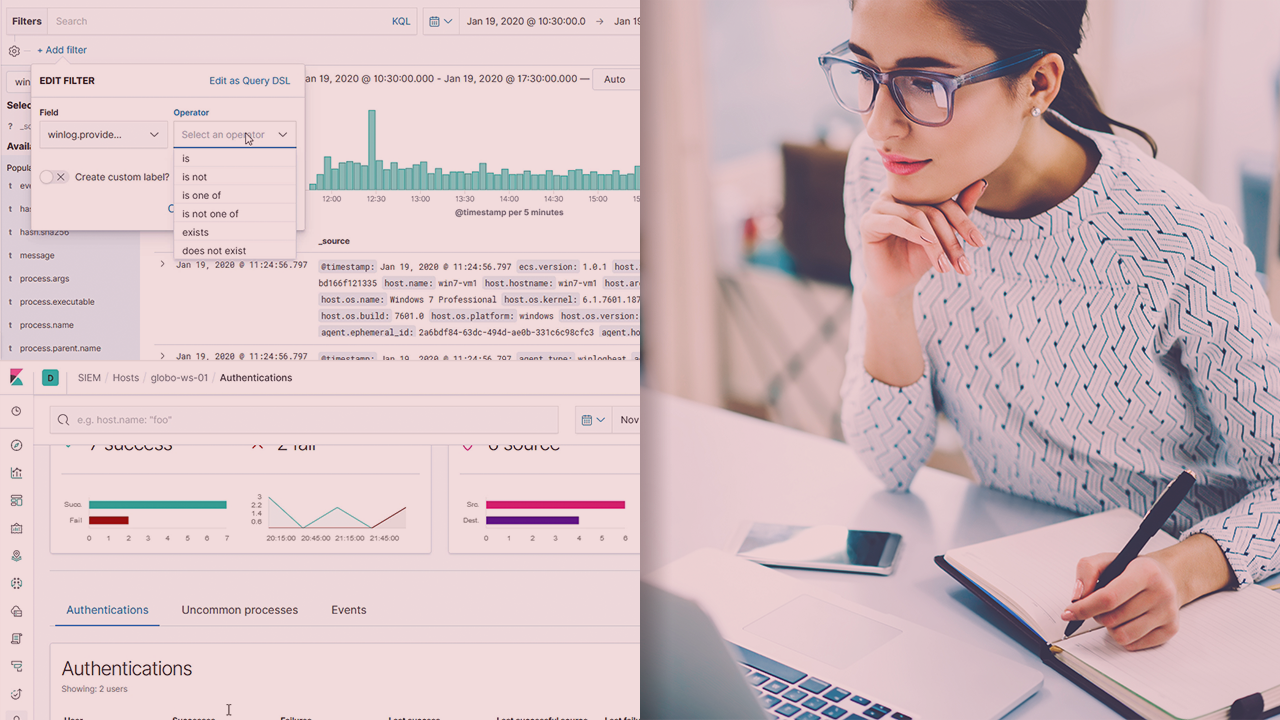
Log parsing and analysis does not scale well to large data sets. This course will teach you how to perform data analysis and baselining on large data sets to efficiently identify and address threats.
- Course
Security Event Triage: Statistical Baselining with SIEM Data Integration
Log parsing and analysis does not scale well to large data sets. This course will teach you how to perform data analysis and baselining on large data sets to efficiently identify and address threats.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
As businesses innovate and make ground-breaking developments in the markets they operate within, successes can become reasons for advanced cyber threats to target your organization. In this course, Security Event Triage: Statistical Baselining with SIEM Data Integration, you will gain the ability to perform detection and analysis of threats at scale. First, you will learn which leg events to look for to identify suspicious activity. Next, you will discover how to pivot between indicators to find the root cause of the incident. Finally, you will explore how to correlate events from multiple sources across your estate to identify the actions on objective of the attacker as well as the impact. When you’re finished with this course, you will have the skills and knowledge of data analysis and baselining needed to detect threats at scale.

