- Course
Security Event Triage: Operationalizing Security Analysis
In this course you begin the security event triage path, entering the world of modern security operations and learning the technologies and skills required by security analysts to be as advanced as the threats they face.
- Course
Security Event Triage: Operationalizing Security Analysis
In this course you begin the security event triage path, entering the world of modern security operations and learning the technologies and skills required by security analysts to be as advanced as the threats they face.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
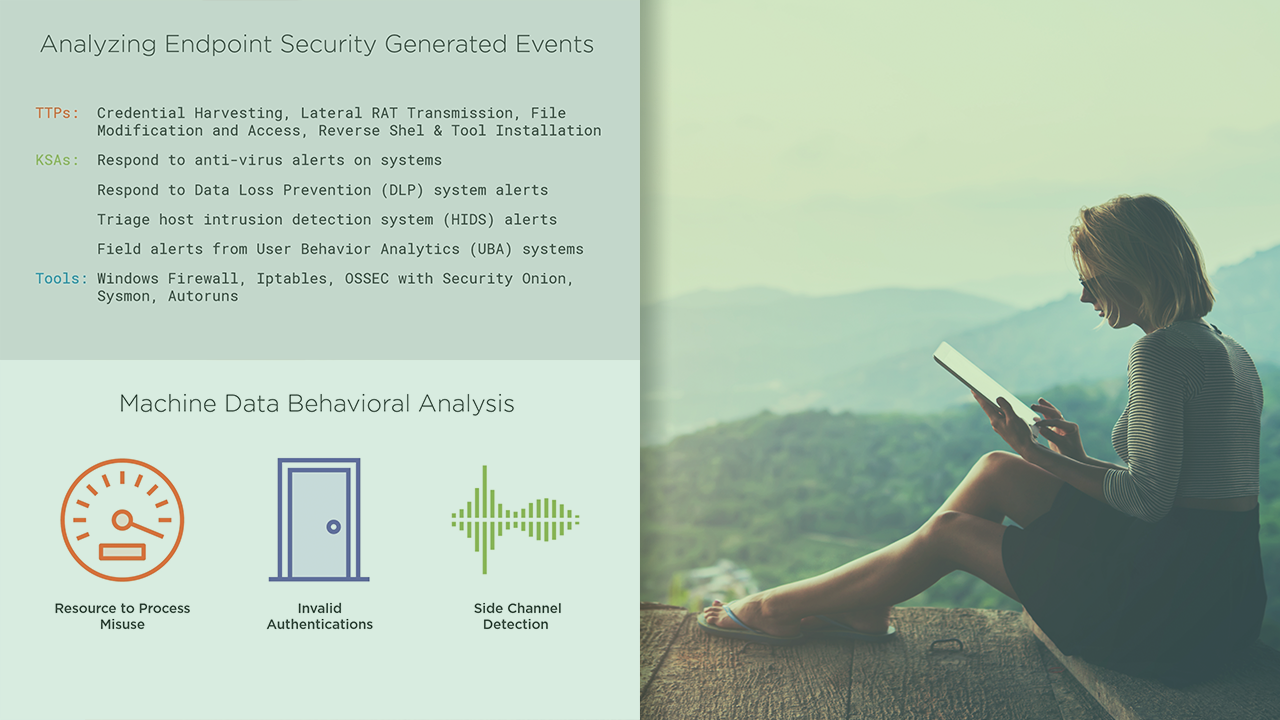
Keeping up with advanced cyber threats and sifting through the insurmountable number of alerts available to security analysts is not sustainable without leveling up your security analysis skills to keep pace with modern security operations. In this course, Security Event Triage: Operationalizing Security Analysis, you will gain foundational knowledge of modern cybersecurity continuous monitoring techniques and processes. First, you will learn how the security analyst fits into the overall cybersecurity posture of an organization. Next, you will discover the technologies and methodologies covered in the security event triage path. Finally, you will map the knowledge, skills, and abilities taught in each of the security event triage courses to the MITRE ATT&CK techniques that comprise the chain of compromise used by the simulated threat actors. When you’re finished with this course, you will have the skills and knowledge of security analysis needed to identify and interrogate all manner of cyber threats.

