- Course
Network Security Monitoring (NSM) with Security Onion
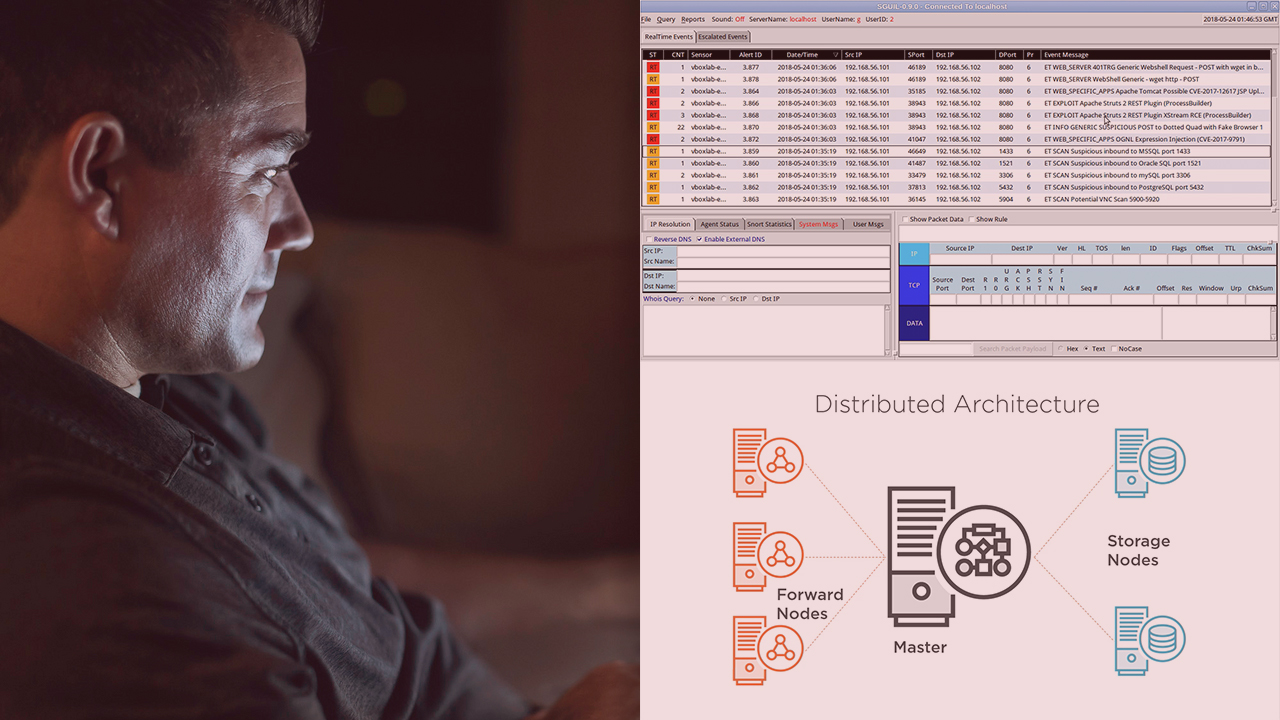
Security Onion is a great Linux distribution built for Network Security Monitoring (NSM). This course will teach you the technical aspects of NSM, as well as the triage process that must be followed, using simulated attacks.
- Course
Network Security Monitoring (NSM) with Security Onion
Security Onion is a great Linux distribution built for Network Security Monitoring (NSM). This course will teach you the technical aspects of NSM, as well as the triage process that must be followed, using simulated attacks.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Network security monitoring is a skill that is at the core of the broad set of skills security professionals can master to prevent, detect, and respond to attacks which are so common today. In this course, Network Security Monitoring (NSM) with Security Onion, you will learn about network security monitoring as well as how to use Security Onion to perform network security monitoring. First, you will learn what NSM is. Next, you will explore where you can deploy network sensors, how to handle the triage process by generating real attacks, how to detect attacks, and how to deploy and operate a Security Onion environment. Finally, you will discover how you can perform network security monitoring in a production environment, and how to deploy your own Security Onion environment and generate attacks to dissect with it. By the end of this course, you will have everything you need to further improve your skills as a security analyst, security engineer, or security architect. These skills are easily transferable to other network security monitoring products, such as commercial ones commonly found in the enterprise.

