- Course
Software and Systems Security for CompTIA CySA+
This course will teach you how to evaluate and look at integrating security into your software and systems.
- Course
Software and Systems Security for CompTIA CySA+
This course will teach you how to evaluate and look at integrating security into your software and systems.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
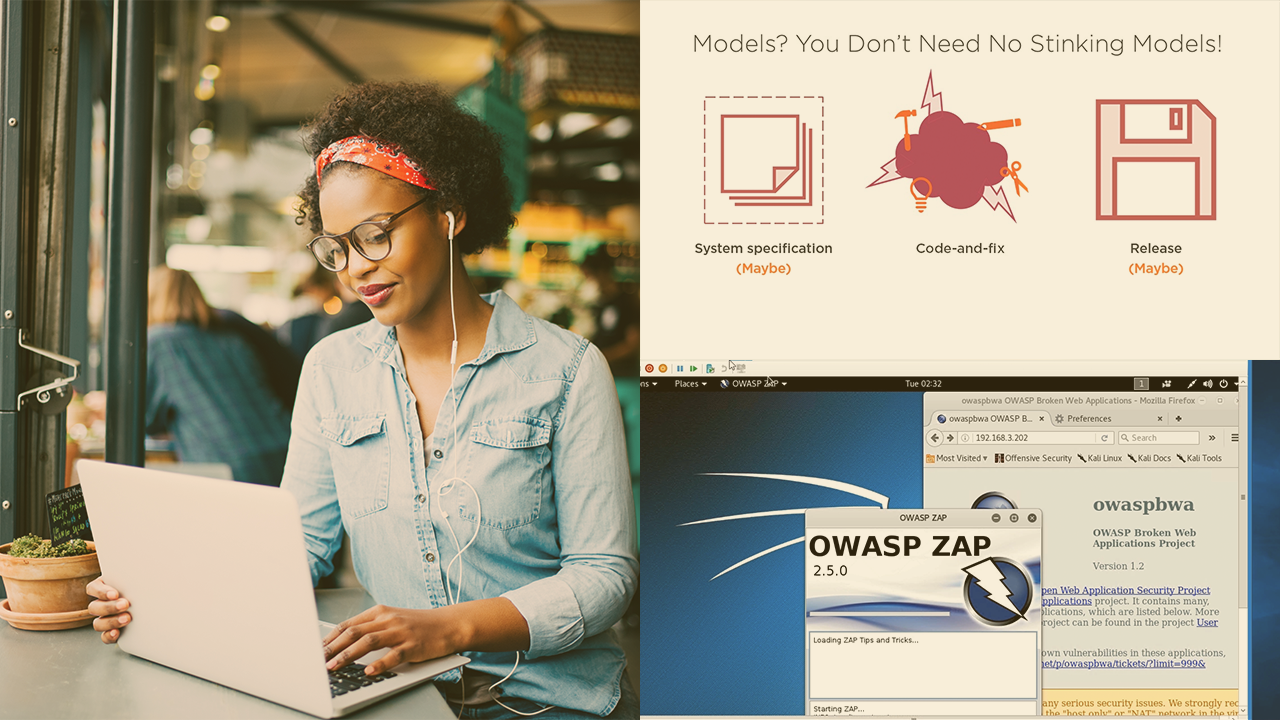
Most companies have a well-oiled machine with the sole purpose to create, release, and maintain functional software. Still, the growing concerns and risks related with insecure software have brought increased attention to the need to mix security into the development process.
In this course, Software and Systems Security for CompTIA CySA+, you’ll learn to evaluate and integrate security within both software and hardware used by your organization.
First, you’ll explore the Software Development Life Cycle (SDLC) and its security implications to make sure that the software your organization uses is well written and secure all throughout its lifespan.
Next, you’ll discover some best practices as you develop applications to make sure security is not overlooked.
Finally, you’ll learn how to make sure any cloud services that you might inject into your environment are secured to be used to support your apps and systems.
When you’re finished with this course, you’ll have the skills and knowledge of security analysis needed to integrate and evaluate your organization’s software and system security profile.
Software and Systems Security for CompTIA CySA+
-
Course Intro: When Dishwashers Attack! | 4m 37s
-
What's the Software Development Lifecycle (SDLC)? | 6m 3s
-
Do We Really Need an SDLC? | 5m 9s
-
Phase 1: Planning | 1m 39s
-
Phase 2: Requirements | 2m 21s
-
Phase 3: Design | 3m 16s
-
Phase 4: Implementation | 1m 19s
-
Phase 5: Testing | 1m 18s
-
Phase 6: Deployment | 2m 26s
-
Phase 7: Maintenance | 59s
-
Phase 8: End of Life | 1m 50s
-
Model: Code and Fix | 2m 3s
-
Model: Waterfalls | 2m 27s
-
Model: Agile | 6m 42s
-
Model: Iterative | 2m 55s
-
Model: Spiral | 2m 36s

