- Course
Suricata 6: Getting Started
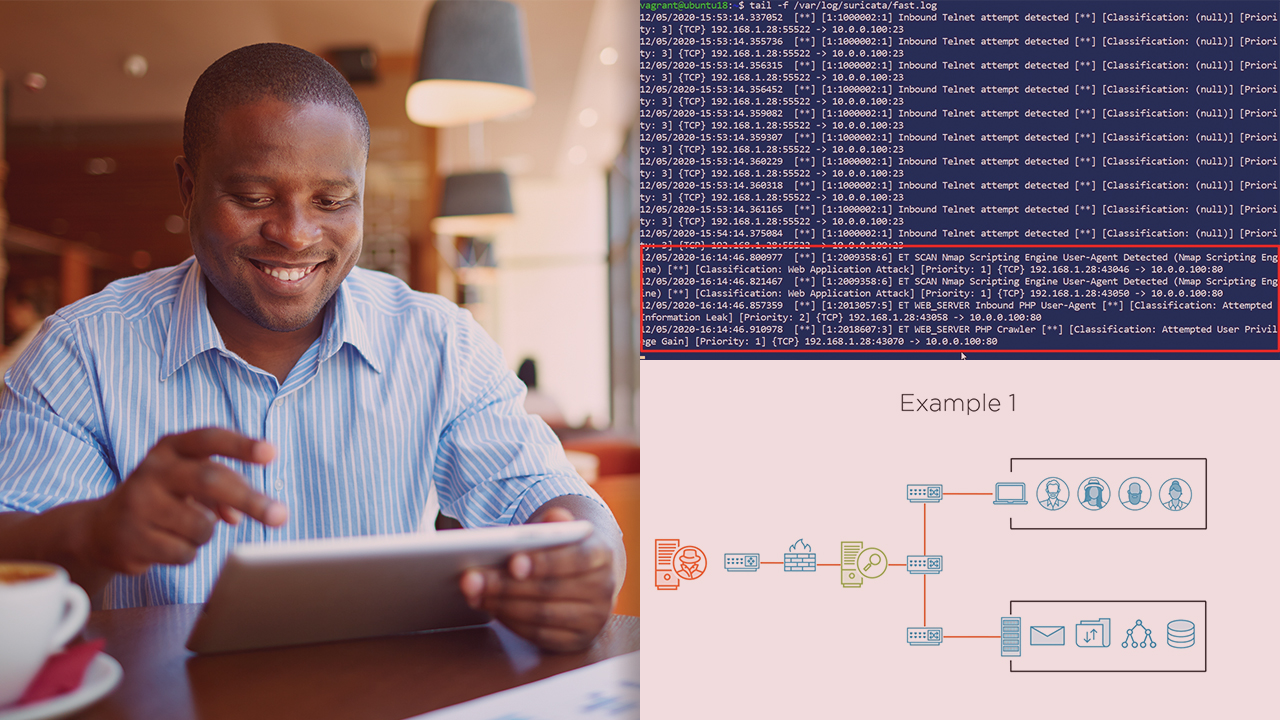
Intrusion detection and prevention are important parts of any enterprise network security monitoring plan. This course will teach you how to install and configure Suricata as an intrusion detection and prevention system.
- Course
Suricata 6: Getting Started
Intrusion detection and prevention are important parts of any enterprise network security monitoring plan. This course will teach you how to install and configure Suricata as an intrusion detection and prevention system.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Intrusion detection and prevention are key in enterprise network security monitoring. In this course, Suricata 6: Getting Started, you’ll learn to install and configure Suricata. First, you’ll explore intrusion detection and prevention fundamentals. Next, you’ll discover how to install Suricata using multiple methods. Finally, you’ll learn how to configure Suricata to capture packets. When you’re finished with this course, you’ll have the skills and knowledge of Suricata needed to install and configure it to capture network traffic.

